60290 Courses
55268 Microsoft Power Automate for End Users
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for The intended audience for this course would be those who have been using Office 365 for some time and are now looking at optimizing their existing business processes and designing new ones. Overview #NAME? This course delivers an instructor-led product showcase for Microsoft Power Automate from start to finish in an engaging and practical way. Power Automate is a diverse product, turning business processes into automated, consistent and visual workPower Automates. Power Automate is designed to interweave the various products in Office 365 as well as connect to other on-premises and web-based solutions. This course will give you the confidence to select the right actions and workPower Automate logic for your business workPower Automates. 1 - AN INTRODUCTION TO POWER AUTOMATE * What is Microsoft Power Automate? * The benefits of automation * How to get to Power Automate * Lab 1: Setup your tenant * Setup Office 365 * Download Course Files * Customise your App Launcher * Create accounts for colleagues * After completing this module, students will be able to: * Know what Microsoft Power Automate is * The Benefits of using Power Automate to automate processes * How to access a Power Automate 2 - GETTING STARTED WITH POWER AUTOMATE * Using Power Automate templates * Navigating in Power Automate * Editing a Power Automate * Publish and trigger a Power Automate * Turn off or delete a Power Automate * Lab 1: Building processes in Office 365 * Create a Team with a channel * Build an absence business process * Testing the absence process * Optional: Create Feedback Form * Optional: Power Automate to Notify of Bad Ratings * Optional: Test your Form and Power Automate * After completing this module, students will be able to: * How to use Power Automate tempaltes * How to navigate around Power Automate * How to edit Power Automates * How to publish and trigger Power Automates * How to turn off or delete Power Automates 3 - POWER AUTOMATE LOGIC * Adding conditions * Designing switches * Using apply to each * Configuring do until logic * Adding a scope * Lab 1: Scheduling documentation reviews * Setup a policy library in SharePoint * Design a policy review schedule * Testing the policy review process * Optional: Notify if a file nears review * After completing this module, students will be able to: * How to add condtions in a Power Automate * How to design switches for a Power Automate * How to use apply to each * How to configure do until logic * How to add a scope 4 - INTEGRATION * Standard and premium connectors * Connecting to web services * Using Power Automate with on-premises data * Lab 1: Using Power Automate and SQL to Review Sales * Create a new orders list * Designing the price check process * Testing the price check process * Optional: Update with managers * After completing this module, students will be able to: * How to use Standard and Premium connectors * How to connect to web services * How to using Power Automate with on-premises data 5 - THE MOBILE APP * Downloading the mobile app * Signing in and account management * Building and managing Power Automates * Creating buttons * Feeds and approvals * Lab 1: Optional: Using the Power Automate mobile app * Setting up the Power Automate mobile app * Create a new Power Automate in the mobile app * Using Power Automate buttons in the app * Uninstall the Power Automate mobile app * After completing this module, students will be able to: * How to download the mobile app * How to sign into the mobile app * How to build and manage Power Automates in the mobile app * How to create buttons in the mobile app * How to feed and use approvals in the mobile app 6 - ADMINISTRATION AND MAINTENANCE * Maintaining a Power Automate * View history and analytics * Sharing a Power Automate * Export and import Power Automates * Office 365 administration for Power Automate * Environments * Data policies * Data integration * Lab 1: Maintaining your Power Automates * Share a Power Automate with a colleague * Disabling an active Power Automate * Deleting a Power Automate * After completing this module, students will be able to: * How to maintain a Power Automate * How to view history and analytics for a Power Automate * How to share a Power Automate * How to export and import Power Automates * How to administrate a Power Automate in Office 365 * How to use data policies in a Power Automate * How to use data integration in a Power Automate

23rd July Laetitia Rutherford #Agent121. Looking for: ADULT FICTION / NON-FICTION
5.0(1)By I Am In Print
LOOKING FOR: ADULT FICTION, ADULT NON-FICTION Laetitia Rutherford is a literary agent at Watson, Little, where she recently passed her ten year anniversary. She began as an agent at Toby Eady Associates, following three years as a Marketing Executive for HarperCollins Fiction. Watson, Little is a longstanding agency representing writers across all tastes and genres and with a strong reputation for extending book rights into Translation and into Film and TV. Laetitia is looking for upmarket and literary Fiction, and for creative Non-Fiction. She welcomes writers from all walks of life and is keen to hear from a variety of voices and life experiences. Laetitia is looking for novels with a strong concept, question or emotional scenario, fresh perspectives, well worked out narratives, and arresting style. She is more often looking for contemporary settings, and loves to be immersed in a distinctive place, but also likes historical novels, as long as they speak lucidly for today. Contemporary issues like housing, money, and the experience of different workplaces appeal, as does unconventional family life and relationships. Laetitia is also open to novels with surreal or fantastical aspects, that throw universal storylines into the challenges of today (and tomorrow)’s complex world. It is always exciting to see a story so relatable, or as yet unheard, or resonant that it speaks to different countries in different languages. Laetitia is experienced in unique literary work, seen in her author Hannah Silva’s My Child, the Algorithm, a Granta Best Books of 2023; gripping and intelligent upmarket fiction (see Anika Scott); as well as highly popular Crime fiction like Ajay Chowdhury’s Detective Kamil Rahman series and Jenny Blackhurst’s locked room refresh Three Card Murder, both in TV development. She loves plot and the puzzle of a really plotty edit, as much as dazzling writing, whether spare or lush. Her current focus is on taking forward Watson, Little’s Literary talent, and less on mainstream Crime. But Laetitia would be excited to see a novel that plays with crime elements – and is looking forward to reading, for example, Jennifer Croft’s The Extinction of Irena Rey. Among the most compelling novels recently read are Fates and Furies by Lauren Groff, No One Is Talking About This by Patricia Lockwood, Girl, Woman, Other by Bernardine Evaristo, The Vanishing Half by Brit Bennett, An American Marriage by Tayeri Jones, Lullaby by Leila Slimani, Lanny by Max Porter, and the William novels by Elizabeth Strout. In Non-Fiction, recent favourites include In the Dream House by Carmen Maria Machado, Maggie Nelson’s The Argonauts, Amy Liptrot’s The Outrun, Jennifer Croft’s Homesick, and Noreen Masud’s A Flat Place. Laetitia would like you to submit a covering letter, 1 page synopsis and the first three chapters or 5,000 words of your manuscript in a single word document. (In addition to the paid sessions, Laetitia is kindly offering one free session for low income/under-represented writers. Please email agent121@iaminprint.co.uk [agent121@iaminprint.co.uk] to apply, outlining your case for this option which is offered at the discretion of I Am In Print). By booking you understand you need to conduct an internet connection test with I Am In Print prior to the event. You also agree to email your material in one document to reach I Am In Print by the stated submission deadline and note that I Am In Print take no responsibility for the advice received during your agent meeting. The submission deadline is: Monday 15 July 2024

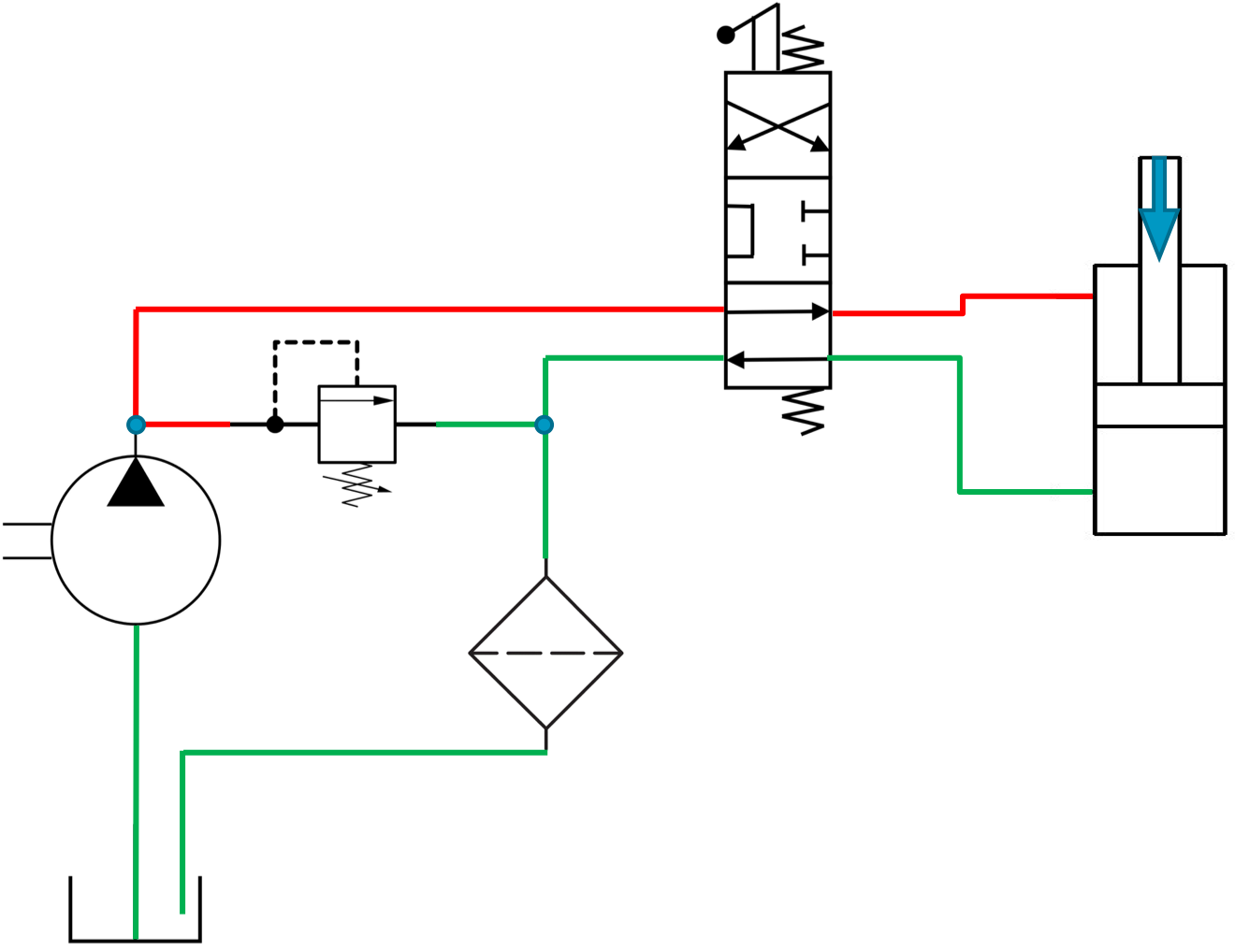
ServiceTech Module 4 - Basic Hydraulics - Small Plant / Hydrostatic Drive Systems
By Learning for Hire Limited
This course covers hydraulic systems - starting with the fundamentals through to ISO Schematics. Ideal for tool hire, plant hire. CPA Members HAE Members and IPAF Members for their Fitters, mechanics, technicians, Check and Test, Test and Run, PDI Techs, not forgetting Charities or other organisations who run maintain or sell hydraulic equipped machinery and those that sell, deal in or refurbish equipment.
CompTIA A+ Part 1
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for individuals who have basic computer user skills and who are interested in obtaining a job as an entry-level IT technician. This course is also designed for students who are seeking the CompTIA A+ certification. Overview Install and configure mobile devices Compare and contrast networking hardware Configure internet connections and wireless networking Troubleshoot hardware and networks Install motherboards, RAM, storage devices, CPUs and add-on cards Deploy and configure connected devices Summarize cloud-computing concepts and virtualization CompTIA A+ certified professionals are proven problem solvers. They support today's core technologies from security to cloud to data management and more. CompTIA A+ is the industry standard for launching IT careers into today's digital world. It is the only industry-recognized credential with performance-based items to prove pros can think on their feet to perform critical IT support tasks in the moment. It is trusted by employers around the world to identify the go-to person in end-point management and technical support roles. CompTIA A+ is regularly re-invented by IT experts to ensure that it validates core skills and abilities demanded in the workplace. Prerequisites While there are no prerequisites for this course, please ensure you have the right level of experience to be successful in this training. LESSON 1: INSTALLING MOTHERBOARDS AND CONNECTORS * Topic 1A: Explain Cable Types and Connectors * Topic 1B: Install and Configure Motherboards * Topic 1C: Explain Legacy Cable Types LESSON 2: INSTALLING SYSTEM DEVICES * Topic 2A: Install and Configure Power Supplies and Cooling * Topic 2B: Select and Install Storage Devices * Topic 2C: Install and Configure System Memory * Topic 2D: Install and Configure CPUs LESSON 3: TROUBLESHOOTING PC HARDWARE * Topic 3A: Apply Troubleshooting Methodology * Topic 3B: Configure BIOS/UEFI * Topic 3C: Troubleshoot Power and Disk Issues * Topic 3D: Troubleshoot System and Display Issues LESSON 4: COMPARING LOCAL NETWORKING HARDWARE * Topic 4A: Compare Network Types * Topic 4B: Compare Networking Hardware * Topic 4C: Explain Network Cable Types * Topic 4D: Compare Wireless Networking Types LESSON 5: CONFIGURING NETWORK ADDRESSING AND INTERNET CONNECTIONS * Topic 5A: Compare Internet Connection Types * Topic 5B: Use Basic TCP/IP Concepts * Topic 5C: Compare Protocols and Ports * Topic 5D: Compare Network Configuration Concepts LESSON 6: SUPPORTING NETWORK SERVICES * Topic 6A: Summarize Services Provided by Networked Hosts * Topic 6B: Compare Internet and Embedded Appliances * Topic 6C: Troubleshoot Networks LESSON 7: SUMMARIZING VIRTUALIZATION AND CLOUD CONCEPTS * Topic 7A: Summarize Client-Side Virtualization * Topic 7B: Summarize Cloud Concepts * Lesson 8: Supporting Mobile Devices * Topic 8A: Set Up Mobile Devices and Peripherals * Topic 8B: Configure Mobile Device Apps * Topic 8C: Install and Configure Laptop Hardware * Topic 8D: Troubleshoot Mobile Device Issues LESSON 9: SUPPORTING PRINT DEVICES * Topic 9A: Deploy Printer and Multifunction Devices * Topic 9B: Replace Print Device Consumables * Topic 9C: Troubleshoot Print Device Issues

SC-100T00 Microsoft Cybersecurity Architect
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for experienced cloud security engineers who have taken a previous certification in the security, compliance and identity portfolio. Specifically, students should have advanced experience and knowledge in a wide range of security engineering areas, including identity and access, platform protection, security operations, securing data, and securing applications. They should also have experience with hybrid and cloud implementations. Beginning students should instead take the course SC-900: Microsoft Security, Compliance, and Identity Fundamentals. This is an advanced, expert-level course. Although not required to attend, students are strongly encouraged to have taken and passed another associate level certification in the security, compliance and identity portfolio (such as AZ-500, SC-200 or SC-300) before attending this class. This course prepares students with the expertise to design and evaluate cybersecurity strategies in the following areas: Zero Trust, Governance Risk Compliance (GRC), security operations (SecOps), and data and applications. Students will also learn how to design and architect solutions using zero trust principles and specify security requirements for cloud infrastructure in different service models (SaaS, PaaS, IaaS). Prerequisites Highly recommended to have attended and passed one of the associate level certifications in the security, compliance and identity portfolio (such as AZ-500T00 Microsoft Azure Security Technologies, SC-200T00: Microsoft Security Operations Analyst, or SC-300T00: Microsoft Identity and Access Administrator.) Advanced experience and knowledge in identity and access, platform protection, security operations, securing data and securing applications. Experience with hybrid and cloud implementations. 1 - INTRODUCTION TO ZERO TRUST AND BEST PRACTICE FRAMEWORKS * Zero Trust initiatives * Zero Trust technology pillars part 1 * Zero Trust technology pillars part 2 2 - DESIGN SOLUTIONS THAT ALIGN WITH THE CLOUD ADOPTION FRAMEWORK (CAF) AND WELL-ARCHITECTED FRAMEWORK (WAF) * Define a security strategy * Cloud Adoption Framework secure methodology * Design security with Azure Landing Zones * The Well-Architected Framework security pillar 3 - DESIGN SOLUTIONS THAT ALIGN WITH THE MICROSOFT CYBERSECURITY REFERENCE ARCHITECTURE (MCRA) AND MICROSOFT CLOUD SECURITY BENCHMARK (MCSB) * Design solutions with best practices for capabilities and controls * Design solutions with best practices for attack protection 4 - DESIGN A RESILIENCY STRATEGY FOR COMMON CYBERTHREATS LIKE RANSOMWARE * Common cyberthreats and attack patterns * Support business resiliency * Ransomware protection * Configurations for secure backup and restore * Security updates 5 - CASE STUDY: DESIGN SOLUTIONS THAT ALIGN WITH SECURITY BEST PRACTICES AND PRIORITIES * Case study description * Case study answers * Conceptual walkthrough * Technical walkthrough 6 - DESIGN SOLUTIONS FOR REGULATORY COMPLIANCE * Translate compliance requirements into a security solution * Address compliance requirements with Microsoft Purview * Address privacy requirements with Microsoft Priva * Address security and compliance requirements with Azure policy * Evaluate infrastructure compliance with Defender for Cloud 7 - DESIGN SOLUTIONS FOR IDENTITY AND ACCESS MANAGEMENT * Design cloud, hybrid and multicloud access strategies (including Azure AD) * Design a solution for external identities * Design modern authentication and authorization strategies * Align conditional access and Zero Trust * Specify requirements to secure Active Directory Domain Services (AD DS) * Design a solution to manage secrets, keys, and certificates 8 - DESIGN SOLUTIONS FOR SECURING PRIVILEGED ACCESS * The enterprise access model * Design identity governance solutions * Design a solution to secure tenant administration * Design a solution for cloud infrastructure entitlement management (CIEM) * Design a solution for privileged access workstations and bastion services 9 - DESIGN SOLUTIONS FOR SECURITY OPERATIONS * Design security operations capabilities in hybrid and multicloud environments * Design centralized logging and auditing * Design security information and event management (SIEM) solutions * Design solutions for detection and response * Design a solution for security orchestration, automation, and response (SOAR) * Design security workflows * Design threat detection coverage 10 - CASE STUDY: DESIGN SECURITY OPERATIONS, IDENTITY AND COMPLIANCE CAPABILITIES * Case study description * Case study answers * Conceptual walkthrough * Technical walkthrough 11 - DESIGN SOLUTIONS FOR SECURING MICROSOFT 365 * Evaluate security posture for collaboration and productivity workloads * Design a Microsoft 365 Defender solution * Design configurations and operational practices for Microsoft 365 12 - DESIGN SOLUTIONS FOR SECURING APPLICATIONS * Design and implement standards to secure application development * Evaluate security posture of existing application portfolios * Evaluate application threats with threat modeling * Design security lifecycle strategy for applications * Secure access for workload identities * Design a solution for API management and security * Design a solution for secure access to applications 13 - DESIGN SOLUTIONS FOR SECURING AN ORGANIZATION'S DATA * Design a solution for data discovery and classification using Microsoft Purview * Design a solution for data protection * Design data security for Azure workloads * Design security for Azure Storage * Design a security solution with Microsoft Defender for SQL and Microsoft Defender for Storage 14 - CASE STUDY: DESIGN SECURITY SOLUTIONS FOR APPLICATIONS AND DATA * Case study description * Case study answers * Conceptual walkthrough * Technical walkthrough 15 - SPECIFY REQUIREMENTS FOR SECURING SAAS, PAAS, AND IAAS SERVICES * Specify security baselines for SaaS, PaaS, and IaaS services * Specify security requirements for web workloads * Specify security requirements for containers and container orchestration 16 - DESIGN SOLUTIONS FOR SECURITY POSTURE MANAGEMENT IN HYBRID AND MULTICLOUD ENVIRONMENTS * Evaluate security posture by using Microsoft Cloud Security Benchmark * Design integrated posture management and workload protection * Evaluate security posture by using Microsoft Defender for Cloud * Posture evaluation with Microsoft Defender for Cloud secure score * Design cloud workload protection with Microsoft Defender for Cloud * Integrate hybrid and multicloud environments with Azure Arc * Design a solution for external attack surface management 17 - DESIGN SOLUTIONS FOR SECURING SERVER AND CLIENT ENDPOINTS * Specify server security requirements * Specify requirements for mobile devices and clients * Specify internet of things (IoT) and embedded device security requirements * Secure operational technology (OT) and industrial control systems (ICS) with Microsoft Defender for IoT * Specify security baselines for server and client endpoints * Design a solution for secure remote access 18 - DESIGN SOLUTIONS FOR NETWORK SECURITY * Design solutions for network segmentation * Design solutions for traffic filtering with network security groups * Design solutions for network posture management * Design solutions for network monitoring 19 - CASE STUDY: DESIGN SECURITY SOLUTIONS FOR INFRASTRUCTURE * Case study description * Case study answers * Conceptual walkthrough * Technical walkthrough ADDITIONAL COURSE DETAILS: Nexus Humans SC-100T00 Microsoft Cybersecurity Architect training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the SC-100T00 Microsoft Cybersecurity Architect course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

SC-200T00 Microsoft Security Operations Analyst
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The Microsoft Security Operations Analyst collaborates with organizational stakeholders to secure information technology systems for the organization. Their goal is to reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders. Responsibilities include threat management, monitoring, and response by using a variety of security solutions across their environment. The role primarily investigates, responds to, and hunts for threats using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security products. Since the Security Operations Analyst consumes the operational output of these tools, they are also a critical stakeholder in the configuration and deployment of these technologies. Learn how to investigate, respond to, and hunt for threats using Microsoft Sentinel, Microsoft Defender for Cloud, and Microsoft 365 Defender. In this course you will learn how to mitigate cyberthreats using these technologies. Specifically, you will configure and use Microsoft Sentinel as well as utilize Kusto Query Language (KQL) to perform detection, analysis, and reporting. The course was designed for people who work in a Security Operations job role and helps learners prepare for the exam SC-200: Microsoft Security Operations Analyst. Prerequisites Basic understanding of Microsoft 365 Fundamental understanding of Microsoft security, compliance, and identity products Intermediate understanding of Windows 10 Familiarity with Azure services, specifically Azure SQL Database and Azure Storage Familiarity with Azure virtual machines and virtual networking Basic understanding of scripting concepts. 1 - INTRODUCTION TO MICROSOFT 365 THREAT PROTECTION * Explore Extended Detection & Response (XDR) response use cases * Understand Microsoft Defender XDR in a Security Operations Center (SOC) * Explore Microsoft Security Graph * Investigate security incidents in Microsoft Defender XDR 2 - MITIGATE INCIDENTS USING MICROSOFT 365 DEFENDER * Use the Microsoft Defender portal * Manage incidents * Investigate incidents * Manage and investigate alerts * Manage automated investigations * Use the action center * Explore advanced hunting * Investigate Microsoft Entra sign-in logs * Understand Microsoft Secure Score * Analyze threat analytics * Analyze reports * Configure the Microsoft Defender portal 3 - PROTECT YOUR IDENTITIES WITH MICROSOFT ENTRA ID PROTECTION * Microsoft Entra ID Protection overview * Detect risks with Microsoft Entra ID Protection policies * Investigate and remediate risks detected by Microsoft Entra ID Protection 4 - REMEDIATE RISKS WITH MICROSOFT DEFENDER FOR OFFICE 365 * Automate, investigate, and remediate * Configure, protect, and detect * Simulate attacks 5 - SAFEGUARD YOUR ENVIRONMENT WITH MICROSOFT DEFENDER FOR IDENTITY * Configure Microsoft Defender for Identity sensors * Review compromised accounts or data * Integrate with other Microsoft tools 6 - SECURE YOUR CLOUD APPS AND SERVICES WITH MICROSOFT DEFENDER FOR CLOUD APPS * Understand the Defender for Cloud Apps Framework * Explore your cloud apps with Cloud Discovery * Protect your data and apps with Conditional Access App Control * Walk through discovery and access control with Microsoft Defender for Cloud Apps * Classify and protect sensitive information * Detect Threats 7 - RESPOND TO DATA LOSS PREVENTION ALERTS USING MICROSOFT 365 * Describe data loss prevention alerts * Investigate data loss prevention alerts in Microsoft Purview * Investigate data loss prevention alerts in Microsoft Defender for Cloud Apps 8 - MANAGE INSIDER RISK IN MICROSOFT PURVIEW * Insider risk management overview * Create and manage insider risk policies * Investigate insider risk alerts * Take action on insider risk alerts through cases * Manage insider risk management forensic evidence * Create insider risk management notice templates 9 - INVESTIGATE THREATS BY USING AUDIT FEATURES IN MICROSOFT DEFENDER XDR AND MICROSOFT PURVIEW STANDARD * Explore Microsoft Purview Audit solutions * Implement Microsoft Purview Audit (Standard) * Start recording activity in the Unified Audit Log * Search the Unified Audit Log (UAL) * Export, configure, and view audit log records * Use audit log searching to investigate common support issues 10 - INVESTIGATE THREATS USING AUDIT IN MICROSOFT DEFENDER XDR AND MICROSOFT PURVIEW (PREMIUM) * Explore Microsoft Purview Audit (Premium) * Implement Microsoft Purview Audit (Premium) * Manage audit log retention policies * Investigate compromised email accounts using Purview Audit (Premium) 11 - INVESTIGATE THREATS WITH CONTENT SEARCH IN MICROSOFT PURVIEW * Explore Microsoft Purview eDiscovery solutions * Create a content search * View the search results and statistics * Export the search results and search report * Configure search permissions filtering * Search for and delete email messages 12 - PROTECT AGAINST THREATS WITH MICROSOFT DEFENDER FOR ENDPOINT * Practice security administration * Hunt threats within your network 13 - DEPLOY THE MICROSOFT DEFENDER FOR ENDPOINT ENVIRONMENT * Create your environment * Understand operating systems compatibility and features * Onboard devices * Manage access * Create and manage roles for role-based access control * Configure device groups * Configure environment advanced features 14 - IMPLEMENT WINDOWS SECURITY ENHANCEMENTS WITH MICROSOFT DEFENDER FOR ENDPOINT * Understand attack surface reduction * Enable attack surface reduction rules 15 - PERFORM DEVICE INVESTIGATIONS IN MICROSOFT DEFENDER FOR ENDPOINT * Use the device inventory list * Investigate the device * Use behavioral blocking * Detect devices with device discovery 16 - PERFORM ACTIONS ON A DEVICE USING MICROSOFT DEFENDER FOR ENDPOINT * Explain device actions * Run Microsoft Defender antivirus scan on devices * Collect investigation package from devices * Initiate live response session 17 - PERFORM EVIDENCE AND ENTITIES INVESTIGATIONS USING MICROSOFT DEFENDER FOR ENDPOINT * Investigate a file * Investigate a user account * Investigate an IP address * Investigate a domain 18 - CONFIGURE AND MANAGE AUTOMATION USING MICROSOFT DEFENDER FOR ENDPOINT * Configure advanced features * Manage automation upload and folder settings * Configure automated investigation and remediation capabilities * Block at risk devices 19 - CONFIGURE FOR ALERTS AND DETECTIONS IN MICROSOFT DEFENDER FOR ENDPOINT * Configure advanced features * Configure alert notifications * Manage alert suppression * Manage indicators 20 - UTILIZE VULNERABILITY MANAGEMENT IN MICROSOFT DEFENDER FOR ENDPOINT * Understand vulnerability management * Explore vulnerabilities on your devices * Manage remediation 21 - PLAN FOR CLOUD WORKLOAD PROTECTIONS USING MICROSOFT DEFENDER FOR CLOUD * Explain Microsoft Defender for Cloud * Describe Microsoft Defender for Cloud workload protections * Enable Microsoft Defender for Cloud 22 - CONNECT AZURE ASSETS TO MICROSOFT DEFENDER FOR CLOUD * Explore and manage your resources with asset inventory * Configure auto provisioning * Manual log analytics agent provisioning 23 - CONNECT NON-AZURE RESOURCES TO MICROSOFT DEFENDER FOR CLOUD * Protect non-Azure resources * Connect non-Azure machines * Connect your AWS accounts * Connect your GCP accounts 24 - MANAGE YOUR CLOUD SECURITY POSTURE MANAGEMENT? * Explore Secure Score * Explore Recommendations * Measure and enforce regulatory compliance * Understand Workbooks 25 - EXPLAIN CLOUD WORKLOAD PROTECTIONS IN MICROSOFT DEFENDER FOR CLOUD * Understand Microsoft Defender for servers * Understand Microsoft Defender for App Service * Understand Microsoft Defender for Storage * Understand Microsoft Defender for SQL * Understand Microsoft Defender for open-source databases * Understand Microsoft Defender for Key Vault * Understand Microsoft Defender for Resource Manager * Understand Microsoft Defender for DNS * Understand Microsoft Defender for Containers * Understand Microsoft Defender additional protections 26 - REMEDIATE SECURITY ALERTS USING MICROSOFT DEFENDER FOR CLOUD * Understand security alerts * Remediate alerts and automate responses * Suppress alerts from Defender for Cloud * Generate threat intelligence reports * Respond to alerts from Azure resources 27 - CONSTRUCT KQL STATEMENTS FOR MICROSOFT SENTINEL * Understand the Kusto Query Language statement structure * Use the search operator * Use the where operator * Use the let statement * Use the extend operator * Use the order by operator * Use the project operators 28 - ANALYZE QUERY RESULTS USING KQL * Use the summarize operator * Use the summarize operator to filter results * Use the summarize operator to prepare data * Use the render operator to create visualizations 29 - BUILD MULTI-TABLE STATEMENTS USING KQL * Use the union operator * Use the join operator 30 - WORK WITH DATA IN MICROSOFT SENTINEL USING KUSTO QUERY LANGUAGE * Extract data from unstructured string fields * Extract data from structured string data * Integrate external data * Create parsers with functions 31 - INTRODUCTION TO MICROSOFT SENTINEL * What is Microsoft Sentinel? * How Microsoft Sentinel works * When to use Microsoft Sentinel 32 - CREATE AND MANAGE MICROSOFT SENTINEL WORKSPACES * Plan for the Microsoft Sentinel workspace * Create a Microsoft Sentinel workspace * Manage workspaces across tenants using Azure Lighthouse * Understand Microsoft Sentinel permissions and roles * Manage Microsoft Sentinel settings * Configure logs 33 - QUERY LOGS IN MICROSOFT SENTINEL * Query logs in the logs page * Understand Microsoft Sentinel tables * Understand common tables * Understand Microsoft Defender XDR tables 34 - USE WATCHLISTS IN MICROSOFT SENTINEL * Plan for watchlists * Create a watchlist * Manage watchlists 35 - UTILIZE THREAT INTELLIGENCE IN MICROSOFT SENTINEL * Define threat intelligence * Manage your threat indicators * View your threat indicators with KQL 36 - CONNECT DATA TO MICROSOFT SENTINEL USING DATA CONNECTORS * Ingest log data with data connectors * Understand data connector providers * View connected hosts 37 - CONNECT MICROSOFT SERVICES TO MICROSOFT SENTINEL * Plan for Microsoft services connectors * Connect the Microsoft Office 365 connector * Connect the Microsoft Entra connector * Connect the Microsoft Entra ID Protection connector * Connect the Azure Activity connector 38 - CONNECT MICROSOFT DEFENDER XDR TO MICROSOFT SENTINEL * Plan for Microsoft Defender XDR connectors * Connect the Microsoft Defender XDR connector * Connect Microsoft Defender for Cloud connector * Connect Microsoft Defender for IoT * Connect Microsoft Defender legacy connectors 39 - CONNECT WINDOWS HOSTS TO MICROSOFT SENTINEL * Plan for Windows hosts security events connector * Connect using the Windows Security Events via AMA Connector * Connect using the Security Events via Legacy Agent Connector * Collect Sysmon event logs 40 - CONNECT COMMON EVENT FORMAT LOGS TO MICROSOFT SENTINEL * Plan for Common Event Format connector * Connect your external solution using the Common Event Format connector 41 - CONNECT SYSLOG DATA SOURCES TO MICROSOFT SENTINEL * Plan for syslog data collection * Collect data from Linux-based sources using syslog * Configure the Data Collection Rule for Syslog Data Sources * Parse syslog data with KQL 42 - CONNECT THREAT INDICATORS TO MICROSOFT SENTINEL * Plan for threat intelligence connectors * Connect the threat intelligence TAXII connector * Connect the threat intelligence platforms connector * View your threat indicators with KQL 43 - THREAT DETECTION WITH MICROSOFT SENTINEL ANALYTICS * What is Microsoft Sentinel Analytics? * Types of analytics rules * Create an analytics rule from templates * Create an analytics rule from wizard * Manage analytics rules 44 - AUTOMATION IN MICROSOFT SENTINEL * Understand automation options * Create automation rules 45 - THREAT RESPONSE WITH MICROSOFT SENTINEL PLAYBOOKS * What are Microsoft Sentinel playbooks? * Trigger a playbook in real-time * Run playbooks on demand 46 - SECURITY INCIDENT MANAGEMENT IN MICROSOFT SENTINEL * Understand incidents * Incident evidence and entities * Incident management 47 - IDENTIFY THREATS WITH BEHAVIORAL ANALYTICS * Understand behavioral analytics * Explore entities * Display entity behavior information * Use Anomaly detection analytical rule templates 48 - DATA NORMALIZATION IN MICROSOFT SENTINEL * Understand data normalization * Use ASIM Parsers * Understand parameterized KQL functions * Create an ASIM Parser * Configure Azure Monitor Data Collection Rules 49 - QUERY, VISUALIZE, AND MONITOR DATA IN MICROSOFT SENTINEL * Monitor and visualize data * Query data using Kusto Query Language * Use default Microsoft Sentinel Workbooks * Create a new Microsoft Sentinel Workbook 50 - MANAGE CONTENT IN MICROSOFT SENTINEL * Use solutions from the content hub * Use repositories for deployment 51 - EXPLAIN THREAT HUNTING CONCEPTS IN MICROSOFT SENTINEL * Understand cybersecurity threat hunts * Develop a hypothesis * Explore MITRE ATT&CK 52 - THREAT HUNTING WITH MICROSOFT SENTINEL * Explore creation and management of threat-hunting queries * Save key findings with bookmarks * Observe threats over time with livestream 53 - USE SEARCH JOBS IN MICROSOFT SENTINEL * Hunt with a Search Job * Restore historical data 54 - HUNT FOR THREATS USING NOTEBOOKS IN MICROSOFT SENTINEL * Access Azure Sentinel data with external tools * Hunt with notebooks * Create a notebook * Explore notebook code

The Generic Instructor Course trains future Instructors in the principles of adult learning. These skills can then be used to teach fellow healthcare professionals at a number of our courses, including ALS, EPALS and NLS.
GIC (Two Day Course) - EPALS/APLS Place - University Hospital Lewisham
5.0(3)By Hunter Clinical Training
The Generic Instructor Course trains future Instructors in the principles of adult learning. These skills can then be used to teach fellow healthcare professionals at a number of our courses, including ALS, EPALS and NLS.
You are only eligible to attend this course if you have been given Instructor Potential (IP'd) on the relevant provider course. You will not be eligible to attend this course without this. **PLEASE ONLY APPLY FOR THE CORRECT ALLOCATION YOU HAVE BEEN GIVEN INSTRUCTOR POTENTIAL FOR!** The Generic Instructor Course trains future Instructors in the principles of adult learning. These skills can then be used to teach fellow healthcare professionals at a number of our courses, including ALS, EPALS and NLS. This course is a joint collaboration between Resuscitation Council UK and the Advanced Life Support Group (ALSG). Around 900 Instructors are trained on this course every year. This course consists of a day of e-learning followed by two days of face-to-face attendance, which will take place in a Resuscitation Council UK Course Centre. Across the two day face-to-face sessions, Candidates will attend a lecture before taking part in practical sessions that cover the teaching modalities required to teach the provider courses. These include approaches to teaching skills acquisition, facilitating simulation, undertaking assessments and providing feedback to candidates. After successful completion of the GIC, Candidates must teach on two provider courses as an Instructor Candidate (IC) within two years of the GIC in order to complete their training and receive their qualification.
“Music is the movement of sound to reach the soul for the education of its virtue.” - Plato -------------------------------------------------------------------------------- Our Singing and Audition Masterclass is one of the highlights of the Academy, and an incredible learning opportunity for anyone looking to improve their singing, get started in musical theatre, and perfect audition pieces in order to start attending casting calls or applying to drama schools. The 2-day Masterclass is taught by two amazing tutors: Kath Harman - Kath studied Professional Dance and Musical Theatre at the Urdang Academy in London, and her career highlights include performing with Dua Lipa at the Brit Awards, and travelling the world with Carnival Cruise Line. Emma Hatton - Emma graduated from LSMT and her big break came in 2009 when she made her West End debut - originating the role of Donna in Dreamboats and Petticoats. Following this triumph, she was cast in We Will Rock You as an understudy for the roles of Scarmouche and Meat. Emma has also played Elphaba in Wicked and has a variety of other on-stage credits. Whatever your experience level, this brilliant course will help you break out of your comfort zone in a supportive environment and walk away with an audition toolkit that you can use to start applying to further education or working in the industry. If you have questions about how industry auditions work, Kath and Emma can demystify the process! While the focus of this course is musical theatre, you can choose to work on songs outside of this genre if you like. Please note: Prior to starting the course, we ask all students to submit two songs they would like to work on to In2Drama's Musical Associate Simon Fraser, who will accompany you on piano during the course. If you’re unsure what songs to pick, don’t worry! Reach out to us at admin@in2drama.com [admin@in2drama.com?subject=Website%20Enquiry] when you make your booking and we can help you choose the best songs for your voice and audition goals. HEADSHOTS AND SHOWREELS While taking part in this masterclass, you will have the chance to purchase optional headshots and a showreel to showcase your talents. Our team will help you capture the very best bits of your performances and a brilliant headshot that you can use to apply for future castings and opportunities. When booking the Summer Academy [https://www.in2drama.com/summer-academy], you can add a showreel to your booking if you choose. WHEN AND WHERE? The Singing and Audition Masterclass takes place in Cranleigh Arts Centre, around 20 minutes from Guildford. The venue has a professional theatre, a sprung dance floor for choreography sessions, dressing rooms, and lots of great areas for filming and multimedia activities, so it's the perfect spot for our aspiring performers to learn in. Thursday 25th - Friday 26th July 2024 In2Drama is split into two groups for age related focus 11-15 year olds: 9am - 12pm 16-21 year olds: 1pm - 4pm Presentation: 4.30pm - 5pm

Search By Location
- Courses in London
- Courses in Birmingham
- Courses in Glasgow
- Courses in Liverpool
- Courses in Bristol
- Courses in Manchester
- Courses in Sheffield
- Courses in Leeds
- Courses in Edinburgh
- Courses in Leicester
- Courses in Coventry
- Courses in Bradford
- Courses in Cardiff
- Courses in Belfast
- Courses in Nottingham