2079 Courses in Ditton
ADVANCED JUNOS SECURITY TRAINING COURSE DESCRIPTION This course provides students with intermediate routing knowledge and configuration examples. The course includes an overview of protocol-independent routing features, load balancing and filter-based forwarding, OSPF, BGP, IP tunneling, and high availability (HA) features. Junos Intermediate Routing (JIR) is an intermediate-level course. WHAT WILL YOU LEARN * Demonstrate the understanding of integrated user firewall. * Implement next generation Layer 2 security features. * Implement virtual routing instances in a security setting. * Utilize Junos tools for troubleshooting Junos security implementations. * Implement IPS policy. ADVANCED JUNOS SECURITY TRAINING COURSE DETAILS * Who will benefit: Individuals responsible for implementing, monitoring, and troubleshooting Junos security components. * Prerequisites: Intro to the Junos Operating System * Duration 5 days ADVANCED JUNOS SECURITY TRAINING COURSE CONTENTS * Junos Layer 2 Packet Handling and Security Features Transparent Mode Security Secure Wire Layer 2 Next Generation Ethernet Switching MACsec Lab 2 Implementing Layer 2 Security * Virtualization Virtualization Overview Routing Instances Logical Systems Lab 3 Implementing Junos Virtual Routing * AppSecure Theory AppSecure Overview AppID Overview AppID Techniques Application System Cache Custom Application Signatures * AppSecure Implementation AppTrack AppFW AppQoS APBR SSL Proxy Lab 4 Implementing AppSecure * Working with Log Director Log Director Overview Log Director Components Installing and setting up Log Director Clustering with the Log Concentrator VM Administrating Log Director Lab 5 Deploying Log Director * Sky ATP Theory Sky ATP Overview Monitoring Sky ATP Analysis and Detection of Malware * Sky ATP Implementation Configuring Sky ATP Installing Sky ATP Analysis and detection of Malware Infected Host Case Study Lab 6 Instructor Led Sky ATP Demo * Implementing UTM UTM Overview AntiSpam AntiVirus Content and Web Filtering Lab 7 Implementing UTM * Introduction to IPS IPS Overview Network Asset Protection Intrusion Attack Methods Intrusion Prevention Systems IPS Inspection Walkthrough IPS Policy and Configuration SRX IPS Requirements IPS Operation Modes Basic IPS Policy Review IPS Rulebase Operations Lab 8 Implementing Basic IPS Policy * SDSN SDSN Overview, Components & Configuration Policy Enforcer Troubleshooting SDSN Use Cases Lab 9 Implementing SDSN * Enforcement, Monitoring, and Reporting User Role Firewall and Integrated User Firewall Overview User Role Firewall Implementation Monitoring User Role Firewall Integrated User Firewall Implementation Monitoring Integrated User Firewall Lab 10 Configure User Role Firewall and Integrated User Firewall * Troubleshooting Junos Security Troubleshooting Methodology Troubleshooting Tools Identifying IPsec Issues Lab 11 Performing Security Troubleshooting Techniques * Appendix A: SRX Series Hardware and Interfaces Branch SRX Platform Overview High End SRX Platform Overview SRX Traffic Flow and Distribution SRX Interfaces

How to identify and mitigate procurement fraud and corruption - IN PERSON
By Global Risk Alliance Ltd
Our training programme will provide those involved at any stage of the process for procuring goods and/or services within their organisations with the knowledge and skillset to identify and mitigate the threat posed by the breadth and multi-layered complexity of procurement fraud and corruption.

OOAD TRAINING COURSE DESCRIPTION A workshop course providing thorough practical knowledge of object oriented analysis and design methods. WHAT WILL YOU LEARN * Perform Systems Analysis with Object Oriented methods. * Identify key classes and objects. * Expand and refine OO problem domain models. * Design Class hierarchies using inheritance and polymorphism. * Design programs with Object Oriented methods. OOAD TRAINING COURSE DETAILS * Who will benefit: System analysts, designers, programmers and project managers. * Prerequisites: It is desirable that delegates have experience of programming in C++/Java or some other OOP language. * Duration 5 days OOAD TRAINING COURSE CONTENTS * What is OO? Classes, objects, messages, encapsulation, associations, inheritance, polymorphism, reusability. * What is Systems Analysis and design? Data flow diagrams, structure diagrams. The OO approach. * OOA The problem domain and object modelling. Identifying classes and objects. Generalisation and inheritance. Defining attributes and methods. * OOD Refining the OOA results. Designing the User Interface. Designing the algorithms and data structures using objects. Designing the methods. * OOP Prototyping. Implementing OOD with OOPs and OOPLs.

M.D.D DATING ADVICE FOR WOMEN WITH VERY LOW CONFIDENCE PACKAGE (DATING ADVICE FOR WOMEN)
4.9(27)By Nia Williams Miss Date Doctor Dating Coach London, Couples Therapy
* Introspective test * Emotional regulation and emotional intelligence training * Help in addressing pain points areas * Full Makeover and beauty treatments * 10 V.I.P confidence building sessions * Personality test * Addressing trauma issues * Personal life coach available daily * Behavioural pattern training * Relationships analysation * Happiness test * Dating advice for low confidence and insecurity triggers * Eradication of negative patterns * Cognitive behavioural therapy https://relationshipsmdd.com/product/dating-advice-for-women-with-very-low-confidence-package/ [https://relationshipsmdd.com/product/dating-advice-for-women-with-very-low-confidence-package/]

Climate science workshop - Climate Fresk
By The C Collective
Join a Climate Fresk Climate science workshop to learn about the causes and effects of climate change through a fun and collaborative experience.

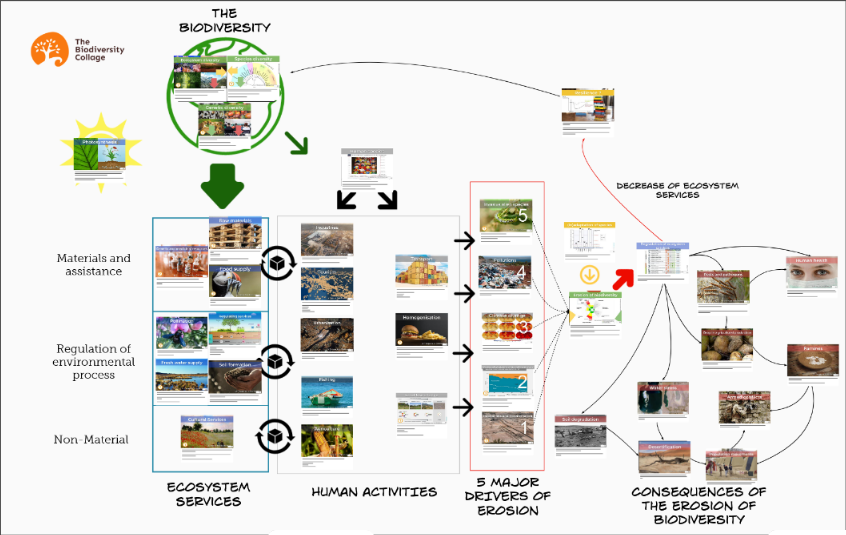
Biodiversity training - Biodiversity collage workshop
By The C Collective
Join a Biodiversity collage workshop to learn about the biodiversity crisis and how to tackle it.
OVERVIEW -------------------------------------------------------------------------------- This is particularly important for PPP projects where long-term commitments are made now based on bankability, value for money and risk allocation. During the course, participants will gain knowledge and skills on the frameworks, tools, and methodologies necessary to build quantitative models for financial decision-making in order to improve the financial viability and bankability of PPP projects. Participants will master modelling frameworks on capital budgeting, risk measurement, regression analysis and Monte Carlo Simulation among others.

OVERVIEW -------------------------------------------------------------------------------- Objectives * Understand the fundamental concepts of credit risk * Evaluate and understand internal and external credit ratings * Understand value at risk (VaR) and its use in measuring credit risk * Explain the counterparty risk for derivatives, particularly over-the-counter derivatives * Describe different credit risk models according to the recommendations of the Basel Committee

OVERVIEW -------------------------------------------------------------------------------- Having a detailed understanding of financial statements is critical to assessing financial risk, and the rate of change in financial statement standards makes this a continuing challenge for users. This course brings together the key elements of financial statement analysis to help participants develop their skills in this area and enable them to ask the right questions to really get under the skin and see the real risks facing businesses and investors in these challenging times. The reference reporting framework used will be IFS.

Search By Location
- Courses in London
- Courses in Birmingham
- Courses in Glasgow
- Courses in Liverpool
- Courses in Bristol
- Courses in Manchester
- Courses in Sheffield
- Courses in Leeds
- Courses in Edinburgh
- Courses in Leicester
- Courses in Coventry
- Courses in Bradford
- Courses in Cardiff
- Courses in Belfast
- Courses in Nottingham