- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Mobile Photography: Take Better Smartphone Photos
By Course Gate
Enhance your mobile photography skills with our comprehensive course. Perfect for hobbyists, content creators, and aspiring photographers. Learn to capture stunning images and elevate your visual storytelling.

Learn Azure Serverless Functions in a Weekend
By Packt
Learn Azure Serverless Computing in a weekend with Azure Functions. This course covers core concepts such as serverless functions, event-driven applications, Azure Service Bus, database interaction, email sending, monitoring, transaction management, integrations, and more! Gain valuable and in-demand skills in Microsoft Azure's Serverless Computing.
Six Sigma White Belt
By Packt
This course teaches you the concepts in bite-sized lectures and helps you understand each aspect of quality, Six Sigma, and the seven quality tools in an easy manner. This course also contains several downloadable templates and real-time data that you will use during your course journey to follow along with the given lectures.

Next.js from Development to Deployment: Build a Music Event Website
By Packt
This course focuses on building the application and static website with the help of Next.js. Next.js is written on JavaScript, therefore, the individual will learn to develop the full-stack application CRUD, pagination, authentication, and more.

Building Microservices API in Go
By Packt
Master Go programming with an in-depth course covering advanced topics such as authentication, authorization, JWT tokens, and refresh tokens. Learn how to write reliable code with effective unit testing techniques, while exploring concepts such as logging, error handling, and modularization. Build secure and scalable web applications with Go to take your coding expertise to the next level.
AWS Certified Data Analytics Specialty (2023) Hands-on
By Packt
This course covers the important topics needed to pass the AWS Certified Data Analytics-Specialty exam (AWS DAS-C01). You will learn about Kinesis, EMR, DynamoDB, and Redshift, and get ready for the exam by working through quizzes, exercises, and practice exams, along with exploring essential tips and techniques.
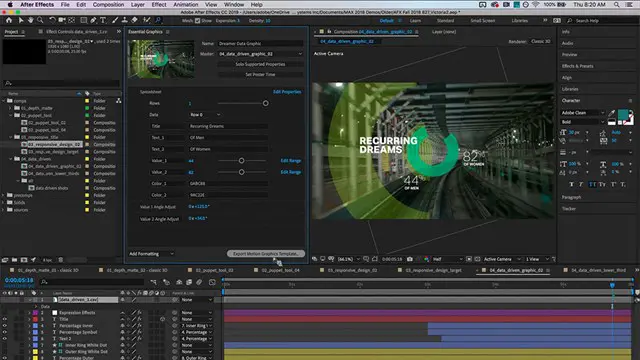
Adobe After Effects Basic to Advanced level training course 1-2-1
By Real Animation Works
AFTEREFFECTS face to face training customised and bespoke.
Practical Cyber Hacking Skills for Beginners
By Packt
Learn theoretical and practical skills in cybersecurity, ethical hacking, cyber management, and develop safe networking principles. We will cover crafting phishing mails, performing brute force attacks, conducting audits with Burp Suite, gather data with Maltego software, and safeguard systems and networks from phishing, malware, ransomware, and social engineering.