324 Management Consulting courses
Get a 10% discount on your first order when you use this promo code at checkout: MAY24BAN3X
CWS-415 Citrix Virtual Apps and Desktops 7 Architect Design Solutions
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is recommended for IT Professionals and Consultants. Overview Identify risks and areas for improvement in a Citrix Virtual Apps and Desktops environment by assessing relevant information in an existing deployment. Determine core Citrix Virtual Apps and Desktops design decisions and align them to business requirements to achieve a practical solution. Design a Citrix Virtual Apps and Desktops disaster recovery plan and understand different disaster recovery considerations. This advanced 5-day training course teaches the design principles for creating a Citrix Virtual Apps and Desktops virtualization solution. In this training, you will also learn how to assess existing environments, explore different scenarios, and make design decisions based on business requirements. This course covers the Citrix Consulting approach to design and covers the key design decisions through lectures, lab exercises, and interactive discussions. You will also learn about additional considerations and advanced configurations for multi-location solutions and disaster recovery planning. This training will help you prepare for the Citrix Certified Expert in Virtualization (CCE-V) exam. MODULE 1: METHODOLOGY & ASSESSMENT * The Citrix Consulting Methodology * Citrix Consulting Methodology Use * Business Drivers * Prioritize Business Drivers * User Segmentation * User Segmentation Process * App Assessment Introduction * App Assessment Analysis * Why Perform a Capabilities Assessment? * Common Capabilities Assessment Risks MODULE 2: USER LAYER * Endpoint Considerations * Peripherals Considerations * Citrix Workspace App Version Considerations * Citrix Workspace App Multiple Version Considerations * Network Connectivity and the User Experience * Bandwidth and Latency Considerations * Graphics Mode Design Considerations * HDX Transport Protocols Considerations * Media Content Redirection Considerations * Session Interruption Management Session Reliability Feature Considerations * Session Interruption Management Auto-Client Reconnect Feature Considerations * Session Interruption Management ICA Keep-Alive Feature Considerations MODULE 3: ACCESS LAYER * Access Matrix * Access Layer * Access Layer Communications * Double-Hop Access Layer Considerations * Citrix Cloud Access Layer Considerations * Use Cases for Multiple Stores * Define Access Paths per User Group * Define Number of URLs * Configuration and Prerequisites for Access Paths * Citrix Gateway Scalability * Citrix Gateway High Availability * StoreFront Server Scalability * StoreFront Server High Availability MODULE 4: RESOURCE LAYER - IMAGES * Flexcast Models * VDA Machine Scalability * VDA Machine Sizing with NUMA * VDA Machine Sizing * VDA Machine Scalability Cloud Considerations * Scalability Testing and Monitoring * Secure VDA Machines Network Traffic * Secure VDA Machines Prevent Breakouts * Secure VDA Machines Implement Hardening * Secure VDA Machines Anti-Virus * Review of Image Methods * Citrix Provisioning Overall Benefits and Considerations * Citrix Provisioning Target Device Boot Methods * Citrix Provisioning Read Cache and Sizing * Citrix Provisioning Write Cache Type * Citrix Provisioning vDisk Store Location * Citrix Provisioning Network Design * Citrix Provisioning Scalability Considerations * Citrix Machine Creation Services Overall Benefits and Considerations * Citrix Machine Creation Services Cloning Types * Citrix Machine Creation Services Storage Locations & Sizing * Citrix Machine Services Read and Write Cache * App Layering Considerations * Image Management Methods MODULE 5: RESOURCE LAYER - APPLICATIONS AND PERSONALIZATION * Application Delivery Option * Determine the Optimal Deployment Method for an App * General Application Concerns * Profile Strategy Profile Types Review * Citrix Profile Management Design Considerations * Citrix Profile Management Scaling * Citrix Profile Management Permissions * Policies Review * Optimize Logon Performance with Policies * Printing Considerations MODULE 6: CONTROL LAYER * Pod Architecture Introduction * Pod Architecture Considerations * Citrix Virtual Apps and Desktops Service Design Considerations * Implement User Acceptance Testing * Load Balancing the Machine Running the VDA * Citrix Director Design Considerations * Management Console Considerations * Change Control * Delivery Controller Scalability and High Availability * Control Layer Security * Configuration Logging Considerations * Session Recording MODULE 7: HARDWARE/COMPUTE LAYER * Hypervisor Host Hardware Considerations * Separating Workloads Considerations * Workload Considerations * VMs Per Host and Hosts Per Pool * Citrix Hypervisor Scalability * VM Considerations in Azure and Amazon Web Services * Storage Tier Considerations * Storage I/O Considerations * Storage Architecture * Storage RAID & Disk Type * Storage Sizing LUNs * Storage Bandwidth * Storage in Public Cloud * Datacenter Networking Considerations * Securing Hypervisor Administrative Access * Secure the Physical Datacenter * Secure the Virtual Datacenter MODULE 8: MODULE 8: HIGH AVAILABILITY AND MULTIPLE LOCATION ENVIRONMENTS * Redundancy vs. Fault Tolerance vs. High Availability * Multi-Location Architecture Considerations * Multi-Site Architecture Considerations * Global Server Load Balancing * Optimal Gateway Routing * Zone Preference and Failover * StoreFront Resource Aggregation * StoreFront Subscription Sync * Hybrid Environment Options * Citrix Provisioning Across Site * Site Database Scalability and High Availability * Citrix Provisioning Across Sites Considerations * Citrix Machine Creation Across Sites * App Layering Across Sites * Managing Roaming Profiles and Citrix Workspace App Configurations Across Devices * Profile Management Multi-Site Replication Considerations * Folder Redirections and Other User Data in a Multi-Location Environment * Application Data Considerations * Cloud-Based Storage Replication Options * Multi-Location Printing Considerations * Zone Considerations * Active Directory Considerations MODULE 9: DISASTER RECOVERY * Tiers of Disaster Recovery * Disaster Recovery Considerations * Business Continuity Planning and Testing * Citrix Standard of Business Continuity

Running Containers on Amazon Elastic Kubernetes Service (Amazon EKS)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is intended for: Those who will provide container orchestration management in the AWS Cloud including: DevOps engineers Systems administrators Overview In this course, you will learn to: Review and examine containers, Kubernetes and Amazon EKS fundamentals and the impact of containers on workflows. Build an Amazon EKS cluster by selecting the correct compute resources to support worker nodes. Secure your environment with AWS Identity and Access Management (IAM) authentication by creating an Amazon EKS service role for your cluster Deploy an application on the cluster. Publish container images to ECR and secure access via IAM policy. Automate and deploy applications, examine automation tools and pipelines. Create a GitOps pipeline using WeaveFlux. Collect monitoring data through metrics, logs, tracing with AWS X-Ray and identify metrics for performance tuning. Review scenarios where bottlenecks require the best scaling approach using horizontal or vertical scaling. Assess the tradeoffs between efficiency, resiliency, and cost and impact for tuning one over the other. Describe and outline a holistic, iterative approach to optimizing your environment. Design for cost, efficiency, and resiliency. Configure the AWS networking services to support the cluster. Describe how EKS/Amazon Virtual Private Cloud (VPC) functions and simplifies inter-node communications. Describe the function of VPC Container Network Interface (CNI). Review the benefits of a service mesh. Upgrade your Kubernetes, Amazon EKS, and third party tools Amazon EKS makes it easy for you to run Kubernetes on AWS without needing to install, operate, and maintain your own Kubernetes control plane. In this course, you will learn container management and orchestration for Kubernetes using Amazon EKS. You will build an Amazon EKS cluster, configure the environment, deploy the cluster, and then add applications to your cluster. You will manage container images using Amazon Elastic Container Registry (ECR) and learn how to automate application deployment. You will deploy applications using CI/CD tools. You will learn how to monitor and scale your environment by using metrics, logging, tracing, and horizontal/vertical scaling. You will learn how to design and manage a large container environment by designing for efficiency, cost, and resiliency. You will configure AWS networking services to support the cluster and learn how to secure your Amazon EKS environment. MODULE 0: COURSE INTRODUCTION * Course preparation activities and agenda MODULE 1: CONTAINER FUNDAMENTALS * Best practices for building applications Container fundamentals Components of a container MODULE 2: KUBERNETES FUNDAMENTALS * Container orchestration Kubernetes objects Kubernetes internals Preparing for Lab 1: Deploying Kubernetes Pods MODULE 3: AMAZON EKS FUNDAMENTALS * Introduction to Amazon EKS Amazon EKS control plane Amazon EKS data plane Fundamentals of Amazon EKS security Amazon EKS API MODULE 4: BUILDING AN AMAZON EKS CLUSTER * Configuring your environment Creating an Amazon EKS cluster Demo: Configuring and deploying clusters in the AWS Management Console Working with eksctl Preparing for Lab 2: Building an Amazon EKS Cluster MODULE 5: DEPLOYING APPLICATIONS TO YOUR AMAZON EKS CLUSTER * Configuring Amazon Elastic Container Registry (Amazon ECR) Demo: Configuring Amazon ECR Deploying applications with Helm Demo: Deploying applications with Helm Continuous deployment in Amazon EKS GitOps and Amazon EKS Preparing for Lab 3: Deploying App MODULE 6: CONFIGURING OBSERVABILITY IN AMAZON EKS * Configuring observability in an Amazon EKS cluster Collecting metrics Using metrics for automatic scaling Managing logs Application tracing in Amazon EKS Gaining and applying insight from observability Preparing for Lab 4: Monitoring Amazon EKS MODULE 7: BALANCING EFFICIENCY, RESILIENCE, AND COST OPTIMIZATION IN AMAZON EKS * The high level overview Designing for resilience Designing for cost optimization Designing for efficiency MODULE 8: MANAGING NETWORKING IN AMAZON EKS * Review: Networking in AWS Communicating in Amazon EKS Managing your IP space Deploying a service mesh Preparing for Lab 5: Exploring Amazon EKS Communication MODULE 9: MANAGING AUTHENTICATION AND AUTHORIZATION IN AMAZON EKS * Understanding the AWS shared responsibility model Authentication and authorization Managing IAM and RBAC Demo: Customizing RBAC roles Managing pod permissions using RBAC service accounts MODULE 10: IMPLEMENTING SECURE WORKFLOWS * Securing cluster endpoint access Improving the security of your workflows Improving host and network security Managing secrets Preparing for Lab 6: Securing Amazon EKS MODULE 11: MANAGING UPGRADES IN AMAZON EKS * Planning for an upgrade Upgrading your Kubernetes version Amazon EKS platform versions ADDITIONAL COURSE DETAILS: Nexus Humans Running Containers on Amazon Elastic Kubernetes Service (Amazon EKS) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Running Containers on Amazon Elastic Kubernetes Service (Amazon EKS) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

VMware Horizon Cloud Service Next Gen on Microsoft Azure: Deploy and Manage
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Horizon Cloud Service on Microsoft Azure administrators, system integrators, account managers, solutions architects, solutions engineers, sales engineers, and consultants. Overview By the end of the course, you should be able to meet the following objectives: Describe the architecture of Horizon Cloud Service on Microsoft Azure Discuss the initial Microsoft Azure configurations required for the Horizon Cloud Service on Microsoft Azure deployment Discuss Horizon Cloud Service on Microsoft Azure networking concepts Discuss Horizon Cloud Service on Microsoft Azure AD requirements and integration best practices Discuss the integration of Workspace ONE Access with Horizon Cloud Service on Microsoft Azure Discuss the requirements for deploying Horizon Cloud Service on Microsoft Azure Demonstrate how to deploy or upgrade Horizon Cloud Service on Microsoft Azure Identify the Horizon Cloud Service console controls that are available to administrators Identify Horizon Cloud upgrade features and benefits List the steps and considerations to take when setting up a primary VM to be used as an assignable image List the steps to install the user software on the primary VM Describe pools and pool groups Explain the creation process and configuration options for single-session and multisession pools and pool groups Create single-session and multisession assignments and entitlements Explain power management options in the multisession pool groups Manage assignable images on Horizon Cloud Service on Microsoft Azure Identify how to access desktops and application from Horizon Cloud Service on Microsoft Azure Describe the integration of VMware Dynamic Environment Manager with Horizon Cloud Service on Microsoft Azure Manage user personalization and application configurations using the VMware Dynamic Environment Manager management console and application profiler Discuss the usage of App Volumes for Horizon Cloud Service on Microsoft Azure Interpret scalability considerations for Horizon Cloud Service on Microsoft Azure Apply troubleshooting techniques relevant to Horizon Cloud Service and Microsoft Azure Summarize the analytics and monitoring capabilities in Horizon Cloud Service on Microsoft Azure This five-day, hands-on training provides you with the knowledge, skills, and abilities to successfully deploy and manage VMware Horizon© Cloud Service? on Microsoft Azure. This training also teaches you how to use the VMware Horizon Cloud administration console and Microsoft Azure portal. Through a combination of hands-on labs and interactive lectures, you learn how to import and manage images for single and multisession assignments. You also learn how to configure and use the Universal Broker function, VMware App Volumes?, VMware Workspace ONE© Access?, and VMware Dynamic Environment Manager? in the Horizon Cloud Service on Microsoft Azure deployment. COURSE INTRODUCTION * Introduction and course logistics * Course objectives INTRODUCTION TO HORIZON CLOUD SERVICE ON MICROSOFT AZURE * Discuss the features and benefits of Horizon Cloud Service on Microsoft Azure * Identify the available Horizon Cloud and Microsoft licensing options * Identify the system architecture components of Horizon Cloud Service on Microsoft Azure * Explain how VMware Dynamic Environment Manager is used in Horizon Cloud profile management * Describe Horizon Cloud application management using App Volumes * Identify the Microsoft Azure configuration prerequisites for a Horizon Cloud integration * Identify the main Microsoft Azure components required for a Horizon Cloud deployment * Review the virtual machines supported in Horizon Cloud Service on Microsoft Azure MICROSOFT AZURE NETWORKING REQUIREMENTS * Discuss Horizon Cloud connectivity considerations and tasks * Explain the networking concepts for Horizon Cloud Service on Microsoft Azure * Identify the ports required for local connections, remote connections, and endpoint OS firewall rules IDENTITY MANAGEMENT * Explain computer identity type and user identity type * Discuss the best practices for Horizon Cloud Service on Microsoft Azure AD integrations * Determine the requirements for Horizon Cloud Service on Microsoft Azure AD * Describe the benefits of integrating Horizon Cloud with Workspace ONE Access * Explain how a user obtains access to an entitled virtual desktop or application from the VMware Workspace ONE© Intelligent Hub catalog * Discuss the importance of binding directory with Workspace ONE Access and setting up custom user attribute synchronization * Discuss the importance of configuring the Remote App Access client in Workspace ONE Access * Demonstrate how to access an entitled Horizon virtual desktop or application in the Workspace ONE Intelligent Hub catalog DEPLOYMENT AND UPGRADES * Explain the steps and requirements for deploying Horizon Cloud Service on Microsoft Azure * Describe the features and benefits of Horizon Edge * Describe the differences between internal and external gateways * Outline the Horizon Universal Console controls available for administrators * Identify the features and benefits of the Horizon Cloud upgrades CREATING IMAGES * Outline the process and configuration choices for setting up primary VMs * Identify the configuration choices for importing primary VMs * List the steps to install the user software on the primary VM * Explain how to convert a configured primary VM to an assignable image * Describe pools and pool groups * List the steps for configuring an image to a pool * List the steps for configuring an image to a pool group POOL GROUPS * Compare dedicated assignments to floating assignments * Outline the steps for creating single-session and multisession assignment * Explain the entitlement of pool groups * Outline the creation process and configuration options for multisession pools and pool groups * Explain the power management selections in the multisession pool groups * Compare the rolling maintenance and loadbalancing options * Identify the actions related to the multisession groups page * Identify the actions to add and assign applications to a user or group * Outline the prerequisites for entitling a multisession assignment ACCESS DESKTOPS AND APPLICATIONS * Identify the different versions of Horizon Client * Describe how to access desktops and remote applications with Horizon Client * Describe how to access desktops and remote applications with a browser * Compare the remote display protocols that are available for Horizon Cloud * Describe the Blast Extreme display protocol codecs * List the ideal applications for each Blast Extreme codec * Describe the Blast Extreme policy configurations MANAGING IMAGES * Describe images * Explain how to manage images VMWARE DYNAMIC ENVIRONMENT MANAGER ON HORIZON CLOUD SERVICE ON MICROSOFT AZURE * Identify the functional areas of VMware Dynamic Environment Manager and their benefits * Explain how to use the VMware Dynamic Environment Manager console and application profiler to manage user personalization and application configurations APP VOLUMES FOR HORIZON CLOUD SERVICE ON MICROSOFT AZURE * Explain how App Volumes works with Horizon Cloud Service on Microsoft Azure * Identify the features and benefits of App Volumes in Horizon Cloud Service on Microsoft Azure * Identify the interface elements of App Volumes in Horizon Cloud Service on Microsoft Azure * Demonstrate how to configure App Volumes in Horizon Cloud Service on Microsoft Azure SCALABILITY CONSIDERATIONS * Recognize the scalability settings for Horizon Cloud Service on Microsoft Azure TROUBLESHOOTING HORIZON CLOUD SERVICE ON MICROSOFT AZURE * Explain the troubleshooting basics for Horizon Cloud Service on Microsoft Azure * Identify the analytics and monitoring capabilities of Horizon Cloud Service on Microsoft Azure * Explain the troubleshooting basics for Horizon Cloud ADDITIONAL COURSE DETAILS: Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware Horizon Cloud Service Next Gen on Microsoft Azure: Deploy and Manage training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware Horizon Cloud Service Next Gen on Microsoft Azure: Deploy and Manage course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Telephone Training - New! - 3CX
By Telephone Trainers Ltd
* Handset Training on Yealink & Fanvil handsets * 3CX Web Client User Training * 3CX Phone App * iOS & Android Mobile Apps * Voicemail User * Receptionist/Switchboard * Supervisor/Agent * 3CX Web Client Admin Training (FREE/SMB/STARTUP) * 3CX Management Console Admin Training (PRO/ENT) * 3CX CFD (Call Flow Designer) **Coming soon! * XIMA CCAAS on 3CX Agent, Realtime, Recording and Reporting

Online Options
Show all 321MD-102T00 Microsoft 365 Endpoint Administrator
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The Microsoft 365 Endpoint Administrator is responsible for deploying, configuring, securing, managing, and monitoring devices and client applications in a corporate setting. Their duties include managing identity, access, policies, updates, and apps. They work alongside the M365 Enterprise Administrator to develop and execute a device strategy that aligns with the requirements of a modern organization. Microsoft 365 Endpoint Administrators should be well-versed in M365 workloads and possess extensive skills and experience in deploying, configuring, and maintaining Windows 11 and later, as well as non-Windows devices. Their role emphasizes cloud services over on-premises management technologies. In this course, students will learn to plan and execute an endpoint deployment strategy using contemporary deployment techniques and implementing update strategies. The course introduces essential elements of modern management, co-management approaches, and Microsoft Intune integration. It covers app deployment, management of browser-based applications, and key security concepts such as authentication, identities, access, and compliance policies. Technologies like Microsoft Entra ID, Azure Information Protection, and Microsoft Defender for Endpoint are explored to protect devices and data. Prerequisites The Modern Desktop Administrator must be familiar with M365 workloads and must have strong skills and experience of deploying, configuring, and maintaining Windows 11 and later, and non-Windows devices. 1 - EXPLORE THE ENTERPRISE DESKTOP * Examine benefits of modern management * Examine the enterprise desktop life-cycle model * Examine planning and purchasing * Examine desktop deployment * Plan an application deployment * Plan for upgrades and retirement 2 - EXPLORE WINDOWS EDITIONS * Examine Windows client editions and capabilities * Select client edition * Examine hardware requirements 3 - UNDERSTAND MICROSOFT ENTRA ID * Examine Microsoft Entra ID * Compare Microsoft Entra ID and Active Directory Domain Services * Examine Microsoft Entra ID as a directory service for cloud apps * Compare Microsoft Entra ID P1 and P2 plans * Examine Microsoft Entra Domain Services 4 - MANAGE MICROSOFT ENTRA IDENTITIES * Examine RBAC and user roles in Microsoft Entra ID * Create and manage users in Microsoft Entra ID * Create and manage groups in Microsoft Entra ID * Manage Microsoft Entra objects with PowerShell * Synchronize objects from AD DS to Microsoft Entra ID 5 - MANAGE DEVICE AUTHENTICATION * Describe Microsoft Entra join * Examine Microsoft Entra join prerequisites limitations and benefits * Join devices to Microsoft Entra ID * Manage devices joined to Microsoft Entra ID 6 - ENROLL DEVICES USING MICROSOFT CONFIGURATION MANAGER * Deploy the Microsoft Configuration Manager client * Monitor the Microsoft Configuration Manager client * Manage the Microsoft Configuration Manager client 7 - ENROLL DEVICES USING MICROSOFT INTUNE * Manage mobile devices with Intune * Enable mobile device management * Explain considerations for device enrollment * Manage corporate enrollment policy * Enroll Windows devices in Intune * Enroll Android devices in Intune * Enroll iOS devices in Intune * Explore device enrollment manager * Monitor device enrollment * Manage devices remotely 8 - EXECUTE DEVICE PROFILES * Explore Intune device profiles * Create device profiles * Create a custom device profile 9 - OVERSEE DEVICE PROFILES * Monitor device profiles in Intune * Manage device sync in Intune * Manage devices in Intune using scripts 10 - MAINTAIN USER PROFILES * Examine user profile * Explore user profile types * Examine options for minimizing user profile size * Deploy and configure folder redirection * Sync user state with Enterprise State Roaming * Configure Enterprise State Roaming in Azure 11 - EXECUTE MOBILE APPLICATION MANAGEMENT * Examine mobile application management * Examine considerations for mobile application management * Prepare line-of-business apps for app protection policies * Implement mobile application management policies in Intune * Manage mobile application management policies in Intune 12 - DEPLOY AND UPDATE APPLICATIONS * Deploy applications with Intune * Add apps to Intune * Manage Win32 apps with Intune * Deploy applications with Configuration Manager * Deploying applications with Group Policy * Assign and publish software * Explore Microsoft Store for Business * Implement Microsoft Store Apps * Update Microsoft Store Apps with Intune * Assign apps to company employees 13 - ADMINISTER ENDPOINT APPLICATIONS * Manage apps with Intune * Manage Apps on non-enrolled devices * Deploy Microsoft 365 Apps with Intune * Additional Microsoft 365 Apps Deployment Tools * Configure Microsoft Edge Internet Explorer mode * App Inventory Review 14 - PROTECT IDENTITIES IN MICROSOFT ENTRA ID * Explore Windows Hello for Business * Deploy Windows Hello * Manage Windows Hello for Business * Explore Microsoft Entra ID Protection * Manage self-service password reset in Microsoft Entra ID * Implement multi-factor authentication 15 - ENABLE ORGANIZATIONAL ACCESS * Enable access to organization resources * Explore VPN types and configuration * Explore Always On VPN * Deploy Always On VPN 16 - IMPLEMENT DEVICE COMPLIANCE * Protect access to resources using Intune * Explore device compliance policy * Deploy a device compliance policy * Explore conditional access * Create conditional access policies 17 - GENERATE INVENTORY AND COMPLIANCE REPORTS * Report enrolled devices inventory in Intune * Monitor and report device compliance * Build custom Intune inventory reports * Access Intune using Microsoft Graph API 18 - DEPLOY DEVICE DATA PROTECTION * Explore Windows Information Protection * Plan Windows Information Protection * Implement and use Windows Information Protection * Explore Encrypting File System in Windows client * Explore BitLocker 19 - MANAGE MICROSOFT DEFENDER FOR ENDPOINT * Explore Microsoft Defender for Endpoint * Examine key capabilities of Microsoft Defender for Endpoint * Explore Windows Defender Application Control and Device Guard * Explore Microsoft Defender Application Guard * Examine Windows Defender Exploit Guard * Explore Windows Defender System Guard 20 - MANAGE MICROSOFT DEFENDER IN WINDOWS CLIENT * Explore Windows Security Center * Explore Windows Defender Credential Guard * Manage Microsoft Defender Antivirus * Manage Windows Defender Firewall * Explore Windows Defender Firewall with Advanced Security 21 - MANAGE MICROSOFT DEFENDER FOR CLOUD APPS * Explore Microsoft Defender for Cloud Apps * Planning Microsoft Defender for Cloud Apps * Implement Microsoft Defender for Cloud Apps 22 - ASSESS DEPLOYMENT READINESS * Examine deployment guidelines * Explore readiness tools * Assess application compatibility * Explore tools for application compatibility mitigation * Prepare network and directory for deployment * Plan a pilot 23 - DEPLOY USING THE MICROSOFT DEPLOYMENT TOOLKIT * Evaluate traditional deployment methods * Set up the Microsoft Deployment Toolkit for client deployment * Manage and deploy images using the Microsoft Deployment Toolkit 24 - DEPLOY USING MICROSOFT CONFIGURATION MANAGER * Explore client deployment using Configuration Manager * Examine deployment components of Configuration Manager * Manage client deployment using Configuration Manager * Plan in-place upgrades using Configuration Manager 25 - DEPLOY DEVICES USING WINDOWS AUTOPILOT * Use Autopilot for modern deployment * Examine requirements for Windows Autopilot * Prepare device IDs for Autopilot * Implement device registration and out-of-the-box customization * Examine Autopilot scenarios * Troubleshoot Windows Autopilot 26 - IMPLEMENT DYNAMIC DEPLOYMENT METHODS * Examine subscription activation * Deploy using provisioning packages * Use Windows Configuration Designer * Use Microsoft Entra join with automatic MDM enrollment 27 - PLAN A TRANSITION TO MODERN ENDPOINT MANAGEMENT * Explore using co-management to transition to modern endpoint management * Examine prerequisites for co-management * Evaluate modern management considerations * Evaluate upgrades and migrations in modern transitioning * Migrate data when modern transitioning * Migrate workloads when modern transitioning 28 - MANAGE WINDOWS 365 * Explore Windows 365 * Configure Windows 365 * Administer Windows 365 29 - MANAGE AZURE VIRTUAL DESKTOP * Examine Azure Virtual Desktop * Explore Azure Virtual Desktop * Configure Azure Virtual Desktop * Administer Azure Virtual Desktop ADDITIONAL COURSE DETAILS: Nexus Humans MD-102T00 : Microsoft 365 Endpoint Administrator training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the MD-102T00 : Microsoft 365 Endpoint Administrator course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

CompTIA A+ Certification (Exams 220-1101 and 220-1102)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is targeted to those seeking A+ Certification and anyone in these roles: IT Support Specialist Helpdesk Technician Field Technician Tier I Support Specialist Desktop Support Specialist Associate Network Engineer Systems Support Technician Junior Systems Administrator Overview At completion of this course, you will be able to: Install and configure end-user devices and software Address connectivity problems Perform basic cybersecurity mitigations Troubleshoot common problems to diagnose and resolve issues Demonstrate basic knowledge of scripting, the cloud, and virtualization CompTIA A+ certified professionals are proven problem solvers. They support today?s core technologies from security to networking to virtualization and more. CompTIA A+ is the industry standard for launching IT careers into today?s digital world. This course, prepares you for the CompTIA A+ Certification exams 220-1101 and 220-1102. LESSON 1: INSTALLING MOTHERBOARDS AND CONNECTORS * Topic 1A: Explain Cable Types and Connectors * Topic 1B: Install and Configure Motherboards * Topic 1C: Explain Legacy Cable Types LESSON 2: INSTALLING SYSTEM DEVICES * Topic 2A: Install and Configure Power Supplies and Cooling * Topic 2B: Select and Install Storage Devices * Topic 2C: Install and Configure System Memory * Topic 2D: Install and Configure CPUs LESSON 3: TROUBLESHOOTING PC HARDWARE * Topic 3A: Apply Troubleshooting Methodology * Topic 3B: Configure BIOS/UEFI * Topic 3C: Troubleshoot Power and Disk Issues * Topic 3D: Troubleshoot System and Display Issues LESSON 4: COMPARING LOCAL NETWORKING HARDWARE * Topic 4A: Compare Network Types * Topic 4B: Compare Networking Hardware * Topic 4C: Explain Network Cable Types * Topic 4D: Compare Wireless Networking Types LESSON 5: CONFIGURING NETWORK ADDRESSING AND INTERNET CONNECTIONS * Topic 5A: Compare Internet Connection Types * Topic 5B: Use Basic TCP/IP Concepts * Topic 5C: Compare Protocols and Ports * Topic 5D: Compare Network Configuration Concepts LESSON 6: SUPPORTING NETWORK SERVICES * Topic 6A: Summarize Services Provided by Networked Hosts * Topic 6B: Compare Internet and Embedded Appliances * Topic 6C: Troubleshoot Networks LESSON 7: SUMMARIZING VIRTUALIZATION AND CLOUD CONCEPTS * Topic 7A: Summarize Client-Side Virtualization * Topic 7B: Summarize Cloud Concepts LESSON 8: SUPPORTING MOBILE DEVICES * Topic 8A: Set Up Mobile Devices and Peripherals * Topic 8B: Configure Mobile Device Apps * Topic 8C: Install and Configure Laptop Hardware * Topic 8D: Troubleshoot Mobile Device Issues LESSON 9: SUPPORTING PRINT DEVICES * Topic 9A: Deploy Printer and Multifunction Devices * Topic 9B: Replace Print Device Consumables * Topic 9C: Troubleshoot Print Device Issues LESSON 10: CONFIGURING WINDOWS * Topic 10A: Configure Windows User Settings * Topic 10B: Configure Windows System Settings LESSON 11: MANAGING WINDOWS * Topic 11A: Use Management Consoles * Topic 11B: Use Performance and Troubleshooting Tools * Topic 11C: Use Command-line Tools LESSON 12: IDENTIFYING OS TYPES AND FEATURES * Topic 12A: Explain OS Types * Topic 12B: Compare Windows Editions LESSON 13: SUPPORTING WINDOWS * Topic 13A: Perform OS Installations and Upgrades * Topic 13B: Install and Configure Applications * Topic 13C: Troubleshoot Windows OS Problems LESSON 14: MANAGING WINDOWS NETWORKING * Topic 14A: Manage Windows Networking * Topic 14B: Troubleshoot Windows Networking * Topic 14C: Configure Windows Security Settings * Topic 14D: Manage Windows Shares LESSON 15: MANAGING LINUX AND MACOS * Topic 15A: Identify Features of Linux * Topic 15B: Identify Features of macOS LESSON 16: CONFIGURING SOHO NETWORK SECURITY * Topic 16A: Explain Attacks, Threats, and Vulnerabilities * Topic 16B: Compare Wireless Security Protocols * Topic 16C: Configure SOHO Router Security * Topic 16D: Summarize Security Measures LESSON 17: MANAGING SECURITY SETTINGS * Topic 17A: Configure Workstation Security * Topic 17B: Configure Browser Security * Topic 17C: Troubleshoot Workstation Security Issues LESSON 18: SUPPORTING MOBILE SOFTWARE * Topic 18A: Configure Mobile OS Security * Topic 18B: Troubleshoot Mobile OS and App Software * Topic 18C: Troubleshoot Mobile OS and App Security LESSON 19: USING SUPPORT AND SCRIPTING TOOLS * Topic 19A: Use Remote Access Technologies * Topic 19B: Implement Backup and Recovery * Topic 19C: Explain Data Handling Best Practices * Topic 19D: Identify Basics of Scripting LESSON 20: IMPLEMENTING OPERATIONAL PROCEDURES * Topic 20A: Implement Best Practice Documentation * Topic 20B: Use Proper Communication Techniques * Topic 20C: Use Common Safety and Environmental Procedures

CompTIA A+
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for individuals who have basic computer user skills and who are interested in obtaining a job as an entry-level IT technician. This course is also designed for students who are seeking the CompTIA A+ certification and who want to prepare for the CompTIA A+ Core 1 220-1101 Certification Exam and the CompTIA A+ Core 2 220-1102 Certification Exam. Overview On course completion, participants will be able to: Support operating systems. Install and configure PC system unit components and peripheral devices. Install, configure, and troubleshoot display and multimedia devices. Install, configure, and troubleshoot storage devices. Install, configure, and troubleshoot internal system components. Install, configure, and maintain operating systems. Maintain and troubleshoot Microsoft Windows. Explain network infrastructure concepts. Configure and troubleshoot network connections. Manage users, workstations, and shared resources. Implement client virtualization and cloud computing. Implement physical security. Secure workstations and data. Troubleshoot workstation security issues. Support and troubleshoot laptops. Support and troubleshoot mobile devices. Install, configure, and troubleshoot print devices. Implement operational procedures. CompTIA A+ certified professionals are proven problem solvers. They support today's core technologies from security to cloud to data management and more. CompTIA A+ is the industry standard for launching IT careers into today's digital world. It is the only industry recognized credential with performance-based items to prove pros can think on their feet to perform critical IT support tasks in the moment. It is trusted by employers around the world to identify the go-to person in end point management and technical support roles. CompTIA A+ is regularly re-invented by IT experts to ensure that it validates core skills and abilities demanded in the workplace. 1 - INSTALLING MOTHERBOARDS AND CONNECTORS * Explain Cable Types and Connectors * Install and Configure Motherboards * Explain Legacy Cable Types 2 - INSTALLING SYSTEM DEVICES * Install and Configure Power Supplies and Cooling * Select and Install Storage Devices * Install and Configure System Memory * Install and Configure CPUs 3 - TROUBLESHOOTING PC HARDWARE * Apply Troubleshooting Methodology * Configure BIOS/UEFI * Troubleshoot Power and Disk Issues * Troubleshoot System and Display Issues 4 - COMPARING LOCAL NETWORKING HARDWARE * Compare Network Types * Compare Networking Hardware * Explain Network Cable Types * Compare Wireless Networking Types 5 - CONFIGURING NETWORK ADDRESSING AND INTERNET CONNECTIONS * Compare Internet Connection Types * Use Basic TCP/IP Concepts * Compare Protocols and Ports * Compare Network Configuration Concepts 6 - SUPPORTING NETWORK SERVICES * Summarize Services Provided by Networked Hosts * Compare Internet and Embedded Appliances * Troubleshoot Networks 7 - SUMMARIZING VIRTUALIZATION AND CLOUD CONCEPTS * Summarize Client-Side Virtualization * Summarize Cloud Concepts 8 - SUPPORTING MOBILE DEVICES * Set Up Mobile Devices and Peripherals * Configure Mobile Device Apps * Install and Configure Laptop Hardware * Troubleshoot Mobile Device Issues 9 - SUPPORTING PRINT DEVICES * Deploy Printer and Multifunction Devices * Replace Print Device Consumables * Troubleshoot Print Device Issues 10 - CONFIGURING WINDOWS * Configure Windows User Settings * Configure Windows System Settings 11 - MANAGING WINDOWS * Use Management Consoles * Use Performance and Troubleshooting Tools * Use Command-line Tools 12 - IDENTIFYING OS TYPES AND FEATURES * Explain OS Types * Compare Windows Editions 13 - SUPPORTING WINDOWS * Perform OS Installations and Upgrades * Install and Configure Applications * Troubleshoot Windows OS Problems 14 - MANAGING WINDOWS NETWORKING * Manage Windows Networking * Troubleshoot Windows Networking * Configure Windows Security Settings * Manage Windows Shares 15 - MANAGING LINUX AND MACOS * Identify Features of Linux * Identify Features of macOS 16 - CONFIGURING SOHO NETWORK SECURITY * Explain Attacks, Threats, and Vulnerabilities * Compare Wireless Security Protocols * Configure SOHO Router Security * Summarize Security Measures 17 - MANAGING SECURITY SETTINGS * Configure Workstation Security * Configure Browser Security * Troubleshoot Workstation Security Issues 18 - SUPPORTING MOBILE SOFTWARE * Configure Mobile OS Security * Troubleshoot Mobile OS and App Software * Troubleshoot Mobile OS and App Security 19 - USING SUPPORT AND SCRIPTING TOOLS * Use Remote Access Technologies * Implement Backup and Recovery * Explain Data Handling Best Practices * Identify Basics of Scripting 20 - IMPLEMENTING OPERATIONAL PROCEDURES * Implement Best Practice Documentation * Use Proper Communication Techniques * Use Common Safety and Environmental Procedures

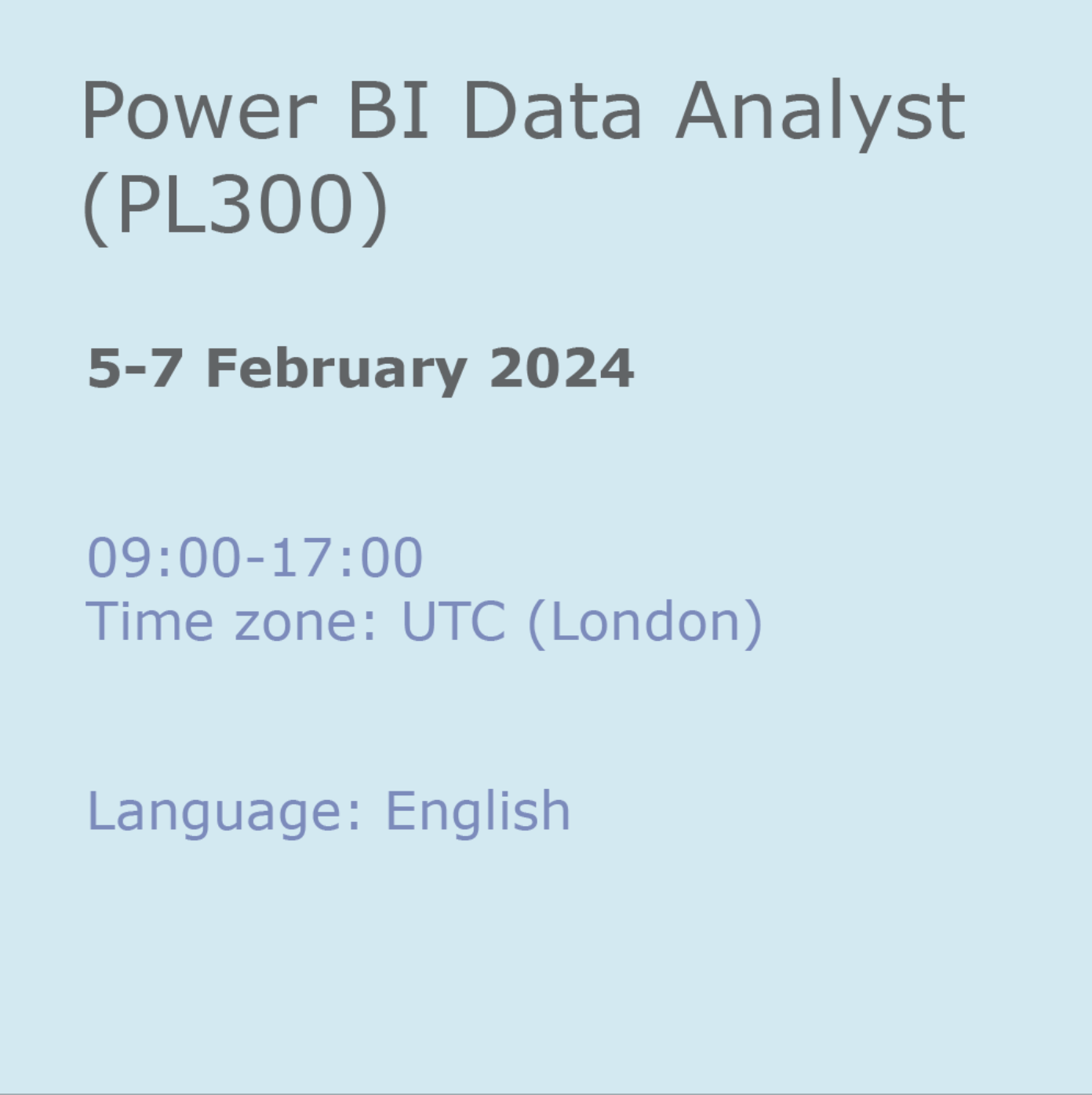
Power BI Data Analyst (PL300)
By Online Productivity Training
OVERVIEW This official Microsoft Power BI training course will teach you how to connect to data from many sources, clean and transform it using Power Query, create a data model consisting of multiple tables connected with relationships and build visualisations and reports to show the patterns in the data. The course will explore formulas created using the DAX language, including the use of advanced date intelligence calculations. Additional visualisation features including interactivity between the elements of a report page are covered as well as parameters and row-level security, which allows a report to be tailored according to who is viewing it. The course will also show how to publish reports and dashboards to a workspace on the Power BI Service. COURSE BENEFITS: * Learn how to clean, transform, and load data from many sources * Use database queries in Power Query to combine tables using append and merge * Create and manage a data model in Power BI consisting of multiple tables connected with relationships * Build Measures and other calculations in the DAX language to plot in reports * Manage advanced time calculations using date tables * Optimise report calculations using the Performance Analyzer * Manage and share report assets to the Power BI Service * Prepare for the official Microsoft PL-300 exam using Microsoft Official Courseware WHO IS THE COURSE FOR? * Data Analysts with little or no experience of Power BI who wish to upgrade their knowledge to include Business Intelligence * Management Consultants who need to conduct rapid analysis of their clients’ data to answer specific business questions * Analysts who need to upgrade their organisation from a simple Excel or SQL-based management reporting system to a dynamic BI system * Data Analysts who wish to develop organisation-wide reporting in the form of web reports or phone apps * Marketers in data-intensive organisations who wish to build visually appealing, dynamic charts for their stakeholders to use COURSE OUTLINE Module 1 Getting Started With Microsoft Data Analytics * Data analytics and Microsoft * Getting Started with Power BI Module 2 Get Data In Power BI * Get data from various data sources * Optimize performance * Resolve data errors Lab: Prepare Data in Power BI Desktop Module 3 Clean, Transform And Load Data In Power BI * Data shaping * Data profiling * Enhance the data structure Lab: Load Data in Power BI Desktop Module 4 Design A Data Model In Power BI * Introduction to data modelling * Working with Tables * Dimensions and Hierarchies Lab: Model Data in Power BI Desktop Module 5 Create Model Calculations Using DAX In Power BI * Introduction to DAX * Real-time Dashboards * Advanced DAX Lab 1: Create DAX Calculations in Power BI Desktop, Part 1 Lab 2: Create DAX Calculations in Power BI Desktop, Part 2 Module 6 Optimize Model Performance * Optimize the data model for performance * Optimize DirectQuery models Module 7 Create Reports * Design a Report * Enhance the Report Lab 1: Design a Report in Power BI Desktop, Part 1 Lab 2: Design a Report in Power BI Desktop, Part 2 Module 8 Create Dashboards * Create a Dashboard * Real-time Dashboards * Enhance a Dashboard Lab: Create a Power BI Dashboard Module 9 Perform Advanced Analytics * Advanced analytics * Data Insights through AI Visuals Lab: Perform Data Analysis in Power BI Desktop Module 10 Create And Manage Workspaces * Creating Workspaces * Sharing and managing assets Module 11 Manage Datasets In Power BI * Parameters * Datasets Module 12 Row-Level Security * Security in Power BI Lab: Enforce Row-Level Security
CompTIA A+ Part 2
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for individuals who have basic computer user skills and who are interested in obtaining a job as an entry-level IT technician. This course is also designed for students who are seeking the CompTIA A+ certification and who want to prepare for the CompTIA A+ Core 2 220-1102 Certification Exam. Overview Identify, install and configure Windows Operating System features Perform OS installations and upgrades Identify features and tools of macOS Identify features and tools of Linux OS Summarize security measures and protocols Configure SOHO network security Manage security settings Troubleshoot Windows OS problems Explain change-management best practices Implement workstation backup and recover methods Identify the basics of scripting CompTIA A+ certified professionals are proven problem solvers. They support today?s core technologies from security to cloud to data management and more. CompTIA A+ is the industry standard for launching IT careers into today?s digital world. It is the only industry recognized credential with performance-based items to prove pros can think on their feet to perform critical IT support tasks in the moment. It is trusted by employers around the world to identify the go-to person in end point management and technical support roles. CompTIA A+ is regularly re-invented by IT experts to ensure that it validates core skills and abilities demanded in the workplace. This course follows after the A+ Part 1 course and prepares you for the A+ Core 2 exam 220-1101. Prerequisites While there are no prerequisites for this course, please ensure you have the right level of experience to be successful in this training. LESSON 1: CONFIGURING WINDOWS * Topic 1A: Configure Windows User Settings * Topic 1B: Configure Windows System Settings LESSON 2: MANAGING WINDOWS * Topic 2A: Use Management Consoles * Topic 2B: Use Performance and Troubleshooting Tools * Topic 2C: Use Command-line Tools LESSON 3: IDENTIFYING OS TYPES AND FEATURES * Topic 3A: Explain OS Types * Topic 3B: Compare Windows Editions LESSON 4: SUPPORTING WINDOWS * Topic 4A: Perform OS Installations and Upgrades * Topic 4B: Install and Configure Application * Topic 4C: Troubleshoot Windows OS Problems LESSON 5: MANAGING WINDOWS NETWORKING * Topic 5A: Manage Windows Networking * Topic 5B: Troubleshoot Windows Networking * Topic 5C: Configure Windows Security Settings * Topic 5D: Manage Windows Shares LESSON 6: MANAGING LINUX AND MACOS * Topic 6A: Identify Features of Linux * Topic 6B: Identify Features of macOS LESSON 7: CONFIGURING SOHO NETWORK SECURITY * Topic 7A: Explain Attacks, Threats, and Vulnerabilities * Topic 7B: Compare Wireless Security Protocols * Topic 7C: Configure SOHO Router Security * Topic 7D: Summarize Security Measures LESSON 8: MANAGING SECURITY SETTINGS * Topic 8A: Configure Workstation Security * Topic 8B: Configure Browser Security * Topic 8C: Troubleshoot Workstation Security Issues LESSON 9: SUPPORTING MOBILE SOFTWARE * Topic 9A: Configure Mobile OS Security * Topic 9B: Troubleshoot Mobile OS and App Software * Topic 9C: Troubleshoot Mobile OS and App Security LESSON 10: USING SUPPORT AND SCRIPTING TOOLS * Topic 10A: Use Remote Access Technologies * Topic 10B: Implement Backup and Recovery * Topic 10C: Explain Data Handling Best Practices * Topic 10D: Identify Basics of Scripting LESSON 11: IMPLEMENTING OPERATIONAL PROCEDURES * Topic 11A: Implement Best Practice Documentation * Topic 11B: Use Proper Communication Techniques * Topic 11C: Use Common Safety and Environmental Procedures

AWS Technical Essentials
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for Individuals responsible for articulating the technical benefits of AWS services Individuals interested in learning how to get started with using AWS SysOps Administrators, Solution Architects and Developers interested in using AWS services Overview Recognize terminology and concepts as they relate to the AWS platform and navigate the AWS Management Console. Understand the foundational services, including Amazon Elastic Compute Cloud (EC2), Amazon Virtual Private Cloud (VPC), Amazon Simple Storage Service (S3), and Amazon Elastic Block Store (EBS). Understand the security measures AWS provides and key concepts of AWS Identity and Access Management (IAM). Understand AWS database services, including Amazon DynamoDB and Amazon Relational Database Service (RDS). Understand AWS management tools, including Auto Scaling, Amazon CloudWatch, Elastic Load Balancing (ELB), and AWS Trusted Advisor. AWS Technical Essentials introduces you to AWS services, and common solutions. It provides you with fundamental knowledge to become more proficient in identifying AWS services. It helps you make informed decisions about IT solutions based on your business requirements and get started working on AWS. Prerequisites * Working knowledge of distributed systems * Familiarity with general networking concepts * Working knowledge of multi-tier architectures * Familiarity with cloud computing concepts 1 - AWS INTRODUCTION AND HISTORY * AWS Global Infrastructure * Demonstration: AWS Management Console 2 - AWS STORAGE * Identify key AWS storage options * Describe Amazon EBS * Create an Amazon S3 bucket and manage associated objects 3 - COMPUTE, NETWORK AND STORAGE SERVICES * Amazon Elastic Compute Cloud (EC2) * Amazon Virtual Private Cloud (VPC) * Amazon Simple Storage Service (S3) * Amazon Elastic Block Store (EBS) * Demonstration: Amazon Simple Storage Service (S3) * Hands-on lab: Build your VPC and launch a web server 4 - AWS SECURITY, AWS IDENTITY AND ACCESS MANAGEMENT (IAM) * AWS Identity and Access Management (IAM) * Demonstration: AWS Identity and Access Management (IAM) 5 - COMPUTE SERVICES & NETWORKING * Identify the different AWS compute and networking options * Describe an Amazon Virtual Private Cloud (VPC) * Create an Amazon EC2 instance * Use Amazon EBS with Amazon EC2 6 - MANAGED SERVICES & DATABASE * Describe Amazon DynamoDB * Understand key aspects of Amazon RDS * Launch an Amazon RDS instance 7 - DATABASES (RDS, DYNAMODB) * SQL and NoSQL databases * Data storage considerations * Hands-on lab: Build your database server and connect to it 8 - AWS ELASTICITY AND MANAGEMENT TOOLS * Auto scaling * Load balancing * Cloud Watch * Trusted Advisor * Hands-on lab: Scale and load balance your architecture 9 - DEPLOYMENT AND MANAGEMENT * Identify what is CloudFormation * Describe Amazon CloudWatch metrics and alarms * Describe Amazon Identity and Access Management (IAM)

50255 Managing Windows Environments with Group Policy
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for Enterprise network staff responsible for help desk support, system administration, and network design. Overview At Course Completion: - Features and functions of Group Policy - Use Group Policy management tools to manage security policies - Design a Group Policy infrastructure - Group Policy processing architecture - Back up, restore, import, and copy Group Policy Objects through the Group Policy - Management Console - Use Windows PowerShell to manage Group Policy - Implement security using Group Policy - Configure the desktop environment with Group Policy - Configure roaming profiles and Folder Redirection - Assign and publish software packages - Implement AppLocker and software restriction policies - Create and deploy Administrative Templates - Configure Group Policy preferences In this course, you will learn how to reduce costs and increase efficiencies in your network. You will discover how to consolidate the administration of an enterprise IT infrastructure with Group Policy, and you will learn to control and manage computer systems and domain users running Windows Server 2016 and Windows clients. Create Group Policies, implement administrative and security templates, and determine best practices when deploying software packages. Walk away with the experience and tools needed to optimize your enterprise systems and networks, implement administrative and security templates, and determine best practices when deploying software packages. 1 - INTRODUCTION TO CONFIGURATION MANAGEMENT * Configuration Management Overview * Configuration Management Using Group Policy * Group Policy Features Introduced with Later Versions of Windows * Using Windows PowerShell in the Configuration Management Process 2 - USING GROUP POLICY MANAGEMENT TOOLS * Local and Domain Policies * Using Group Policy Management Console * Understanding Group Policy Refresh 3 - DESIGNING A GROUP POLICY INFRASTRUCTURE * Design Stages for a Group Policy Infrastructure * Planning your Group Policy Design * Designing Your Group Policy Solution * Deploying Your Group Policy Solution * Managing Your Group Policy Solution 4 - UNDERSTANDING THE ARCHITECTURE OF GROUP POLICY PROCESSING * Group Policy Components in AD DS * Understanding the Group Policy Deployment Order * Modifying Group Policy Processing 5 - TROUBLESHOOTING AND BACKING UP GPOS * Using Group Policy Troubleshooting Tools * Integration of RSoP Functionality * Group Policy Logging Options * Backing Up, Restoring, Importing, and Copying GPOs * Building Migration Tables 6 - SECURING WINDOWS USING GROUP POLICY * Exploring the Windows Security Architecture * Securing User Accounts * Exploring Security Policies * Windows Firewall with Advanced Security * Implementing Domain Security * Security Policy Options for Window Client and Windows Server 7 - IMPLEMENTING APPLICATION SECURITY USING GROUP POLICY * Managing UAC Settings * Defending Against Malware * Using AppLocker to Restrict Software * Implementing Windows App Security Settings 8 - CONFIGURING THE DESKTOP ENVIRONMENT WITH GROUP POLICY * Exploring Script Types and Controlling Script Execution * Defining the Desktop, Start Menu, and Taskbar Settings * Defining the Control Panel Settings * Defining the Windows Components Settings * Configuring the Printer Management and Pruning Settings * Defining the Network Settings * Discovering the new Group Policy Settings 9 - IMPLEMENTING USER STATE VIRTUALIZATION * Configuring Folder Redirection * Managing Offline Files * Implementing User Experience Virtualization * OneDrive for Business 10 - ASSIGNING AND PUBLISHING SOFTWARE PACKAGES * Using MSI Packages to Distribute Software * Using Group Policy as a Software Deployment Method * Deploying Software * Setting Up Distribution Points * Using the Systems Center Configuration Manager to Distribute Software 11 - CONFIGURATION MANAGEMENT WITH WINDOWS POWERSHELL * Introducing Windows PowerShell * Using Windows PowerShell * Writing PowerShell Scripts * Windows PowerShell Library for Group Policy * Windows PowerShell-Based Logon Scripts 12 - IMPLEMENTING POWERSHELL DESIRED STATE CONFIGURATION * Introducing Group Policy Preferences * Comparing Preferences and Policy Settings * Options for Applying Preferences * Configure Preference Settings 13 - CONFIGURING GROUP POLICY PREFERENCES * Introducing Group Policy Preferences * Comparing Preferences and Policy Settings * Options for Applying Preferences * Configuring Preferences Settings ADDITIONAL COURSE DETAILS: Nexus Humans 50255 Managing Windows Environments with Group Policy training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the 50255 Managing Windows Environments with Group Policy course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Business Acumen For Leaders
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for Professionals desiring to improve their business planning, financial management, and decision-making skills and practice them in an ethical and professional manner will benefit from this course. Overview Recognize the importance of the big picture in business planning Leverage financial information to make sound business decisions Identify the importance of other financial levers to your business Understand the importance of ethics on long-term business success Appreciate how business etiquette affects your organizational success Students will learn to understand the mechanics of the organization ? reading and interpreting financials, making sound business decisions, and setting a course ? while also developing the skills to guide and direct your workforce. Private classes on this topic are available. We can address your organization?s issues, time constraints, and save you money, too. Contact us to find out how. 1. GAINING A WIDER PERSPECTIVE * Understanding Business Acumen * Improving Long and Short Term Interactions * Finding and Recognizing Growth Opportunities * Making Mindful Decisions * How to Relate to Others 2. UNDERSTANDING THE NUMBERS * Developing, Defining, and Reporting Key Performance Indicators (KPIs) * Keeping Up with the Business * Understanding Sales, Costs, and Profit Margin * Monitoring Assets, Liabilities, Equity, and Financial Ratios * Reviewing Income Statements, Balance Sheets, and Cash Flow Statements 3. MANAGEMENT CONSIDERATIONS * Recognizing Talent and Organizational Management * Thinking Critically - Asking the Right Questions, Evaluating the Situation, and Making the Decision * Leveraging the Organization - Investing in Employees and Customers, Process Improvement, and Goal Alignment 4. BUSINESS ETHICS * Ensuring Ethical Obligations are Met * Understanding Roles and Responsibilities * Balancing Personal and Organizational Ethics * Managing Ethically - Maintaining the 4 P\'s 5. BUSINESS ETIQUETTE * Maintaining Etiquette across Communication Platforms - Email, IMs, and Telephone * Following Etiquette in Meetings * Delivering Etiquette in Customer Interactions

Exploration Project Management
By Asia Edge
ABOUT THIS VIRTUAL INSTRUCTOR LED TRAINING (VILT) Conducted in an interactive manner, Exploration Project Management will include presentations by the course leader, syndicate and plenary exercises, and (optional) assessment of selected participants' projects. Industry case studies will be integrated into all the presentations. The course material will include a course manual (handout) and a course workbook (for exercises). Participants are requested to bring a mini-poster (two PowerPoint slides) as background material for discussion during the course. Training Objectives By the end of this Virtual Instructor Led Training (VILT), participants will be able to: 1. Improve the evaluation, execution and delivery of exploration projects, measured in terms of successful bids for new acreage, increased success rate and volume delivery from exploration drilling, and more rapid progress in appraisal of discoveries. 2. Describe concepts, simple processes, workflows and analysis tools for project execution. Tools include the expert course leader's proprietary project management framework, including project framing and after-action review methodologies, templates for strategy development, decision trees, decision quality frameworks. They also include customised Excel spreadsheets for portfolio modelling, project risk assessment (in new ventures and prospect maturation) and business planning. 3. Understand their role in (a) delivering the company's strategy, (b) contributing data and assessments to key exploration decision makers, and (c) communicating project progress and results to senior management. Target Audience The Virtual Instructor Led Training (VILT) is aimed at exploration professionals with more than 5 to 10 years of experience in the business, who would like to develop their skills for managing exploration projects and presenting the goals and results of their project work to senior management. * Exploration and engineering professionals who work in exploration project teams, across the spectrum from new ventures (exploration business development), prospect identification and maturation, and appraisal of discoveries * Exploration project leaders * Exploration managers The VILT will also benefit professionals from well engineering, petroleum engineering, finance and planning who support exploration activities. Participants are requested to bring a mini-poster (two PowerPoint slides, each printed on A3 paper) as background material for discussion during the course. Course Level * Basic or Foundation Trainer Your expert course leader draws on more than 35 years of experience managing, reviewing and directing projects in all aspects of the exploration business: from exploration business development (new ventures), through prospect maturation and drilling, to the appraisal of discoveries. He has more than 30 years' experience with Shell International, followed by 10 years consulting to NOCs in Asia Pacific, Africa and South America and independent oil companies in the United Kingdom, continental Europe and North America. Other than delivering industry training, he has worked on projects for oil & gas companies of all sizes, including independents, national oil companies and (super)-majors, private equity firms, hedge funds and investment banks, and leading management consulting firms. He is an alumnus of Cambridge University. He has M.A and Ph.D. degrees in geology and is a Fellow of the Geological Society of London as well as a respected speaker on management panels at international conferences. Professional Experience * Management consultancy & executive education: Advice to investment banks, businesses and major consulting firms. Specialist expertise in upstream oil & gas, with in depth experience in exploration strategy, portfolio valuation and risk assessment. * Leadership: Managed and led teams and departments ranging from 3 - 60 in size. Provided technical leadership to a cadre of 800 explorationists in Shell worldwide. Member of the 12-person VP team leading global exploration in Shell, a $3 bln p.a. business and recognised as the most effective and successful among its industry peers. * Accountability & decision-making: Accountable for bottom-line results: in a range of successful exploration ventures with budgets ranging from $10's million to $100's million. Made, or contributed to, complex business decisions / investments, taking into account strategic, technical, commercial, organisational and political considerations. * Corporate governance: Served as non-executive director on the Boards of the South Rub al Khali Company (oversight of gas exploration studies and drilling in Saudi Arabia) and SEAPOS B.V. (exploration deep-water drilling and facilities management). * Technical & operations: Skilled in exploration opportunity evaluation, the technical de risking of prospects, portfolio analysis and managing the interface between exploration and well engineering activities. Unparalleled knowledge of the oil and gas basins of the world, and of different operating regimes and contractual structures, ranging from Alaska, Gulf of Mexico and Brazil, through to the Middle East, former Soviet Union, Far East and Australia. * Safety: Following an unsatisfactory audit, became accountable for safety performance in Shell's exploration new ventures. Through personal advocacy and leadership of a small team, delivered pragmatic and effective HSE systems, tools and staff training / engagement and a dramatically improved safety record. * R&D: Experience in the 3 key roles in R&D: scientific researcher, research manager, and 'customer' for R&D products. After re-defining Shell's exploration R&D strategy, led the re-structuring of the R&D organization, its interface with 'the business' and approaches to deployment and commercialization. * Strategy: Accomplished at formulating competitive strategies in business, R&D and technology deployment, translating them into actionable tactics and results. Defined the exploration strategy of PDO (a Shell subsidiary in Oman) and latterly of Shell's global exploration programme. * Professional education, behavioural/motivational coaching: Experienced in organisational re-design, change management, leadership education and talent development. * Commercial skills: Personally negotiated drilling compensation claims, educational contracts and E&P contracts, with values of $5 million to $100+ million. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

Best Practice in Portfolio Management in Upstream Oil and Gas
By Asia Edge
ABOUT THIS VIRTUAL INSTRUCTOR LED TRAINING (VILT) This 4 half-day Virtual Instructor Led Training (VILT) course presents the principles and best practices of portfolio management in the upstream (E&P) oil and gas industry. The VILT course is equally valuable for small independents, large integrated international companies and national oil companies. The VILT course consists of presentations, case studies, illustrative practical exercises and syndicate discussions. Particular emphasis is given to pragmatic portfolio management approaches and solutions which can be implemented swiftly without recourse to major investments in planning and portfolio management software. The VILT course will draw on examples from your expert course leader's 35+ years' experience in the oil and gas industry as an explorationist, upstream vice-president and management consultant. The VILT course handout will comprise softcopy slides used in the presentation and a softcopy workbook for the exercises. Participants will gain proficiency in portfolio management techniques, understand how and why to undertake this activity and be able to apply key concepts directly in the business of their teams / divisions. The VILT course will be presented over 4 half-days, using Microsoft Teams or Zoom and a proprietary set of VILT tools. Participants will be asked to complete a pre course questionnaire (PCQ) addressing their objectives and experience, and attend a session to familiarise themselves with VILT tools before course commencement. Training Objectives To present the tools, concepts and principles of portfolio management * To define the quantitative metrics which are used to describe projects in a portfolio * To understand the benefits of portfolio management at different stages of the upstream business: in strategy development, opportunity screening, business development, drilling prospects, conducting appraisal of discoveries and developing fields * To put portfolio management in the organisational context by describing the role of the portfolio management team and examining how value assurance (quality control) is best conducted on portfolio data for projects and assets * To demonstrate how portfolio management contributes to improved business performance By the end of the VILT course, participants will understand: * Key concepts and principles of portfolio management * How to design a simple portfolio database and describe complex projects in a small number of objective metrics * How to segment the portfolio into meaningful units * How to use portfolio data in making business choices and decisions at the strategic and tactical levels * The extent to which it is meaningful and reasonable to make comparisons across different portfolio segments * How the portfolio management team can support the wider business in decision-making Target Audience This VILT course is specially designed for exploration and development geoscientists, E&P economists and finance staff, and E&P managers. Both technical and non-technical staff will benefit from the concepts presented. Companies are encouraged to send participants from different functions and seniority levels to gain great benefits especially those which would like to implement the concepts presented in this VILT course. Course Level * Basic or Foundation Training Methods The VILT course will be delivered online in 4 half-day sessions comprising 4 hours per day, with 2 breaks of 10 minutes per day. The VILT course will be presented in an interactive workshop format that allows for discussion. Course Duration: 4 half-day sessions, 4 hours per session (16 hours in total). Trainer Your expert course leader draws on more than 35 years of experience managing, reviewing and directing projects in all aspects of the exploration business: from exploration business development (new ventures), through prospect maturation and drilling, to the appraisal of discoveries. He has more than 30 years' experience with Shell International, followed by 10 years consulting to NOCs in Asia Pacific, Africa and South America and independent oil companies in the United Kingdom, continental Europe and North America. Other than delivering industry training, he has worked on projects for oil & gas companies of all sizes, including independents, national oil companies and (super)-majors, private equity firms, hedge funds and investment banks, and leading management consulting firms. He is an alumnus of Cambridge University. He has M.A and Ph.D. degrees in geology and is a Fellow of the Geological Society of London as well as a respected speaker on management panels at international conferences. Professional Experience * Management consultancy & executive education: Advice to investment banks, businesses and major consulting firms. Specialist expertise in upstream oil & gas, with in depth experience in exploration strategy, portfolio valuation and risk assessment. * Leadership: Managed and led teams and departments ranging from 3 - 60 in size. Provided technical leadership to a cadre of 800 explorationists in Shell worldwide. Member of the 12-person VP team leading global exploration in Shell, a $3 bln p.a. business and recognised as the most effective and successful among its industry peers. * Accountability & decision-making: Accountable for bottom-line results: in a range of successful exploration ventures with budgets ranging from $10's million to $100's million. Made, or contributed to, complex business decisions / investments, taking into account strategic, technical, commercial, organisational and political considerations. * Corporate governance: Served as non-executive director on the Boards of the South Rub al Khali Company (oversight of gas exploration studies and drilling in Saudi Arabia) and SEAPOS B.V. (exploration deep-water drilling and facilities management). * Technical & operations: Skilled in exploration opportunity evaluation, the technical de risking of prospects, portfolio analysis and managing the interface between exploration and well engineering activities. Unparalleled knowledge of the oil and gas basins of the world, and of different operating regimes and contractual structures, ranging from Alaska, Gulf of Mexico and Brazil, through to the Middle East, former Soviet Union, Far East and Australia. * Safety: Following an unsatisfactory audit, became accountable for safety performance in Shell's exploration new ventures. Through personal advocacy and leadership of a small team, delivered pragmatic and effective HSE systems, tools and staff training / engagement and a dramatically improved safety record. * R&D: Experience in the 3 key roles in R&D: scientific researcher, research manager, and 'customer' for R&D products. After re-defining Shell's exploration R&D strategy, led the re-structuring of the R&D organization, its interface with 'the business' and approaches to deployment and commercialization. * Strategy: Accomplished at formulating competitive strategies in business, R&D and technology deployment, translating them into actionable tactics and results. Defined the exploration strategy of PDO (a Shell subsidiary in Oman) and latterly of Shell's global exploration programme. * Professional education, behavioural/motivational coaching: Experienced in organisational re-design, change management, leadership education and talent development. * Commercial skills: Personally negotiated drilling compensation claims, educational contracts and E&P contracts, with values of $5 million to $100+ million. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

Educators matching "Management Consulting"
Show all 700Search By Location
- Management Consulting Courses in London
- Management Consulting Courses in Birmingham
- Management Consulting Courses in Glasgow
- Management Consulting Courses in Liverpool
- Management Consulting Courses in Bristol
- Management Consulting Courses in Manchester
- Management Consulting Courses in Sheffield
- Management Consulting Courses in Leeds
- Management Consulting Courses in Edinburgh
- Management Consulting Courses in Leicester
- Management Consulting Courses in Coventry
- Management Consulting Courses in Bradford
- Management Consulting Courses in Cardiff
- Management Consulting Courses in Belfast
- Management Consulting Courses in Nottingham








